Would you like to learn how to configure a group policy to enable the BitLocker encryption without a TPM chip? In this tutorial, we will show you how to allow the Operating System encryption using Bitlocker on a computer without the TPM chip using a GPO.
TPM stands for Trusted Platform Module.
• Windows 2012 R2
• Windows 2016
• Windows 2019
• Windows 10
• Windows 7
Equipment list
The following section presents the list of equipment used to create this tutorial.
As an Amazon Associate, I earn from qualifying purchases.
Windows Related Tutorial:
On this page, we offer quick access to a list of tutorials related to Windows.
Tutorial GPO - Enable the BitLocker encryption without a TPM chip
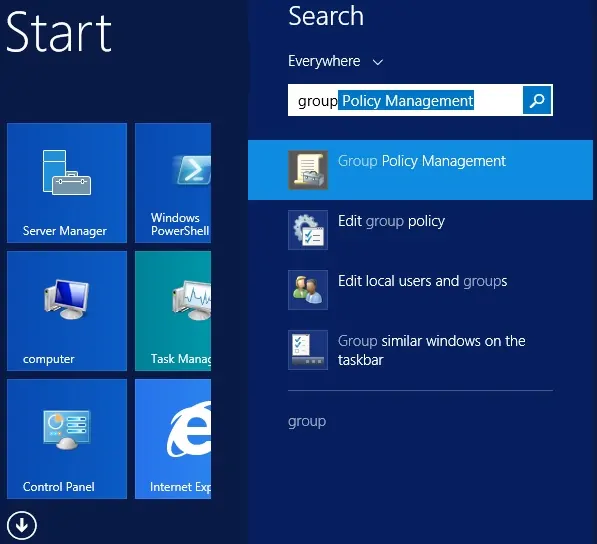
On the domain controller, open the group policy management tool.
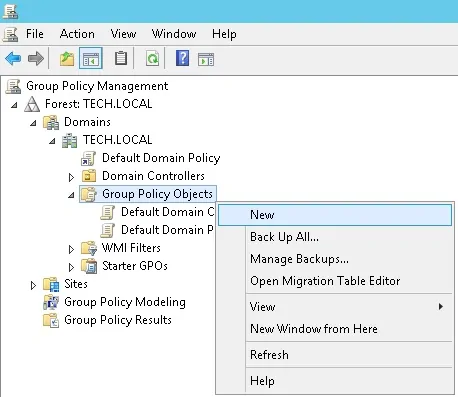
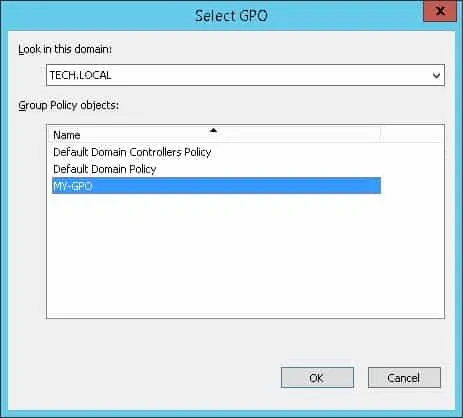
Create a new group policy.
Enter a name for the new group policy.
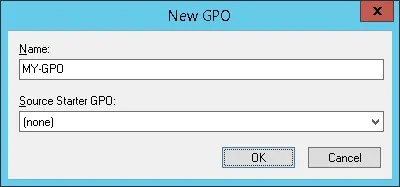
In our example, the new GPO was named: MY-GPO.
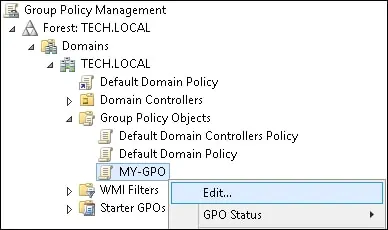
On the Group Policy Management screen, expand the folder named Group Policy Objects.
Right-click your new Group Policy Object and select the Edit option.
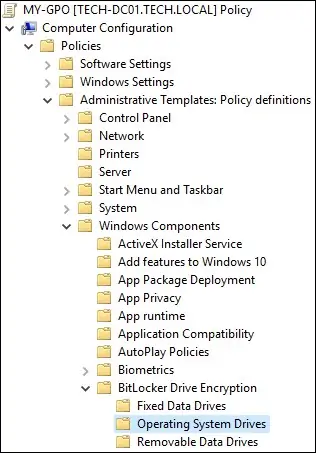
On the group policy editor screen, expand the Computer configuration folder and locate the following item.
Access the folder named Operating System Drives.
Enable the item named: Require additional authentication at startup.
Click on the OK button.
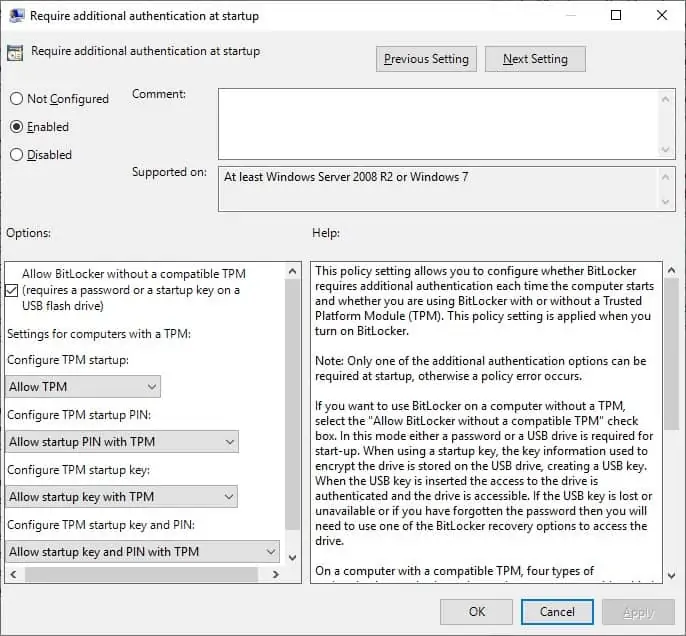
To save the group policy configuration, you need to close the Group Policy editor.
Congratulations! You have finished the GPO creation.
Tutorial - Applying the GPO to allow the BitLocker encryption without a TPM chip
On the Group policy management screen, you need to right-click the Organizational Unit desired and select the option to link an existent GPO.
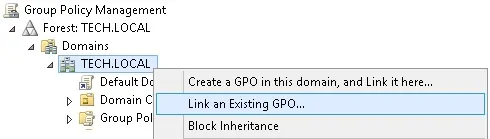
In our example, we are going to link the group policy named MY-GPO to the root of the domain.
After applying the GPO you need to wait for 10 or 20 minutes.
During this time the GPO will be replicated to other domain controllers.
On a remote computer without TPM, try to encrypt the Operating System drive.
In our example, we enabled the BitLocker encryption without a TPM chip using a GPO.