Would you like to learn how to configure iDrac LDAP authentication on Active directory? In this tutorial, we are going to show you how to authenticate iDrac users using the Active directory database from Microsoft Windows and the LDAP over SSL protocol.
• iDrac 8
• Windows 2012 R2
Important! Keep in mind that only LDAP over SSL is supported.
First, we are going to teach you how to install the Active directory and enable the LDAP over SSL feature on the Active directory server.
Copyright © 2018-2026 by Techexpert.tips.
All rights reserved. No part of this publication may be reproduced, distributed, or transmitted in any form or by any means without the prior written permission of the publisher.
Equipment list
Here you can find the list of equipment used to create this tutorial.
This link will also show the software list used to create this tutorial.
Dell iDRAC Playlist:
On this page, we offer quick access to a list of videos related to Dell iDRAC.
Don't forget to subscribe to our youtube channel named FKIT.
Dell iDRAC Related Tutorial:
On this page, we offer quick access to a list of tutorials related to Dell iDRAC.
Tutorial - Active Directory Installation on Windows
• IP - 192.168.15.10.
• Operacional System - Windows 2012 R2
• Hostname - TECH-DC01
• Active Directory Domain: TECH.LOCAL
If you already have an Active Directory domain, you may skip this part of the tutorial.
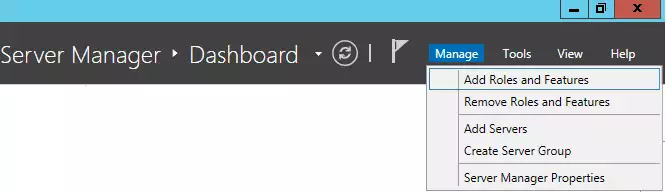
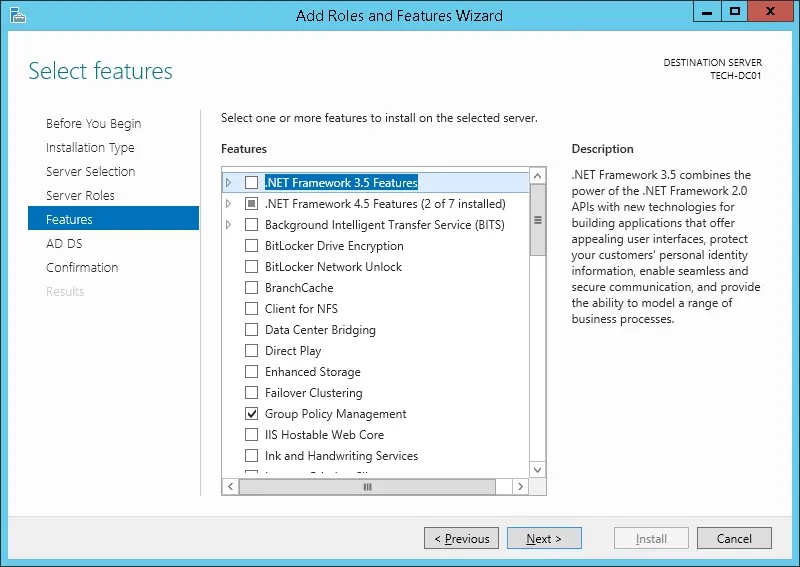
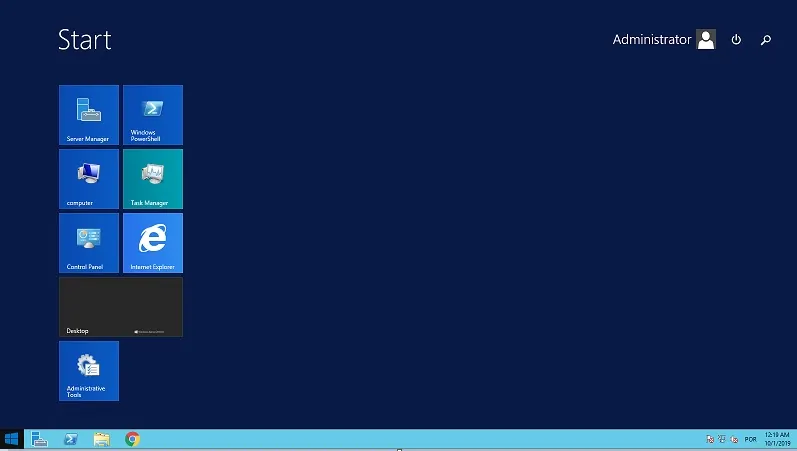
Open the Server Manager application.
Access the Manage menu and click on Add roles and features.
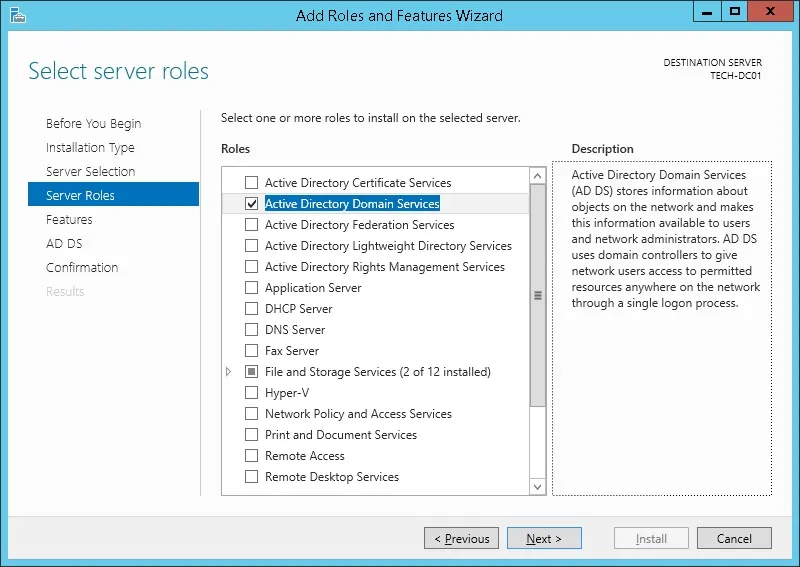
Access the Server role screen, select the Active Directory Domain Service and click on the Next button.
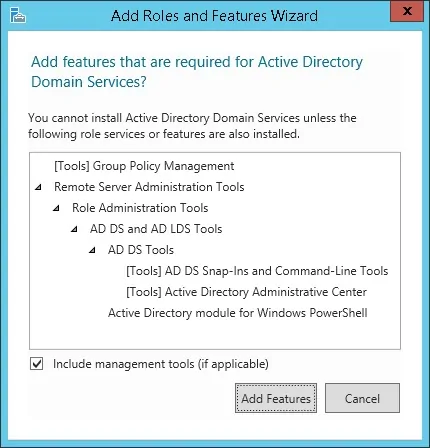
On the following screen, click on the Add features button.
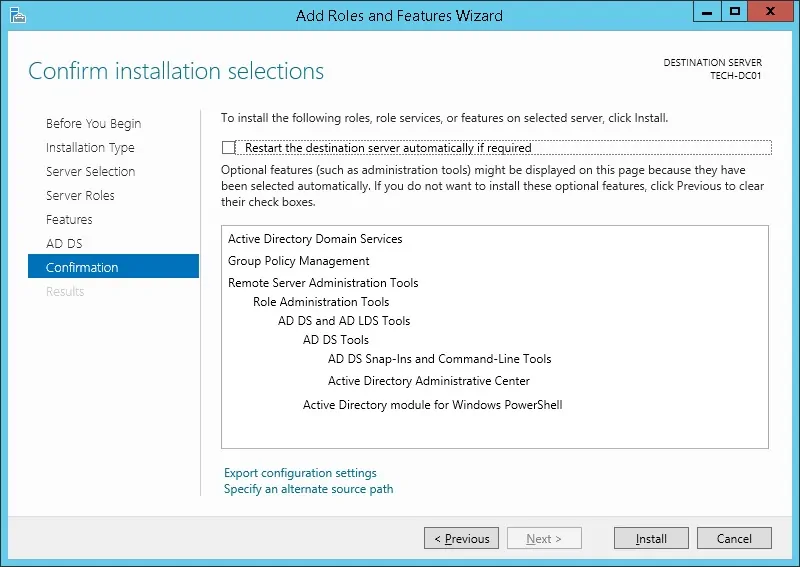
Keep clicking on the Next button until you reach the last screen.
On the confirmation screen, click on the Install button.
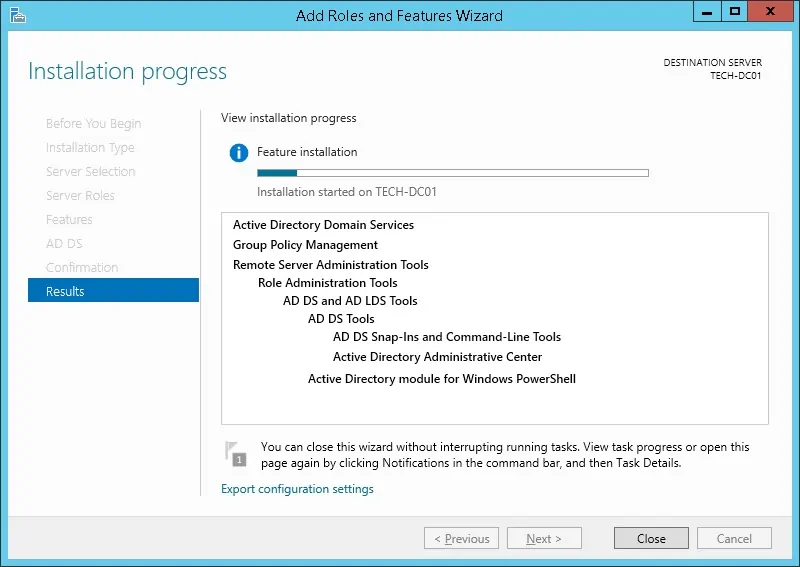
Wait the Active directory installation to finish.
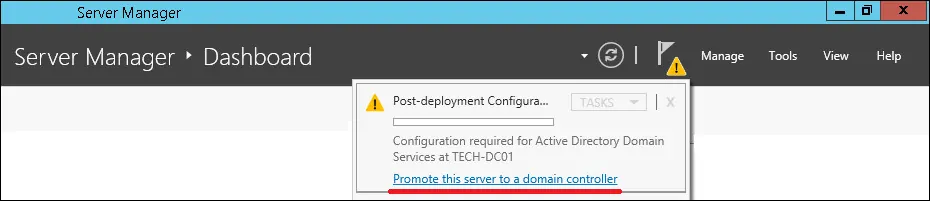
Open the Server Manager application.
Click on the yellow flag menu and select the option to promote this server to a domain controller
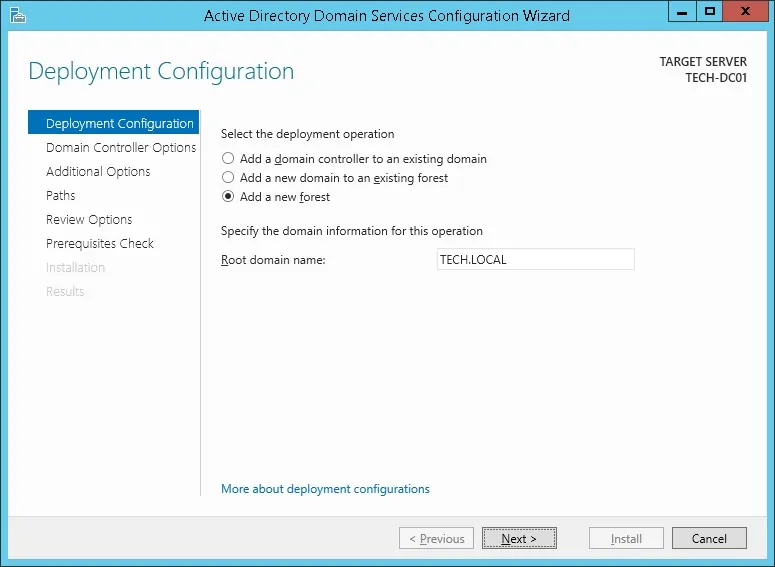
Select the option to Add a new forest and enter a root domain name.
In our example, we created a new domain named: TECH.LOCAL.
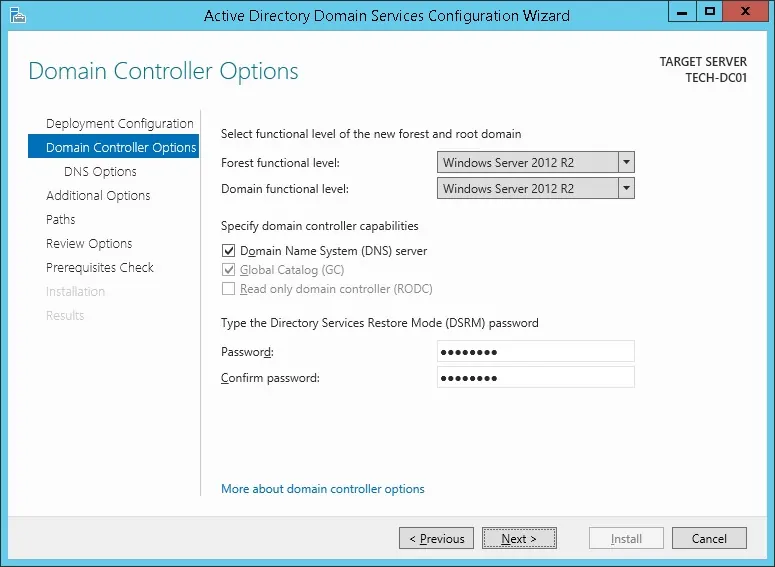
Enter a password to secure the Active Directory restoration.
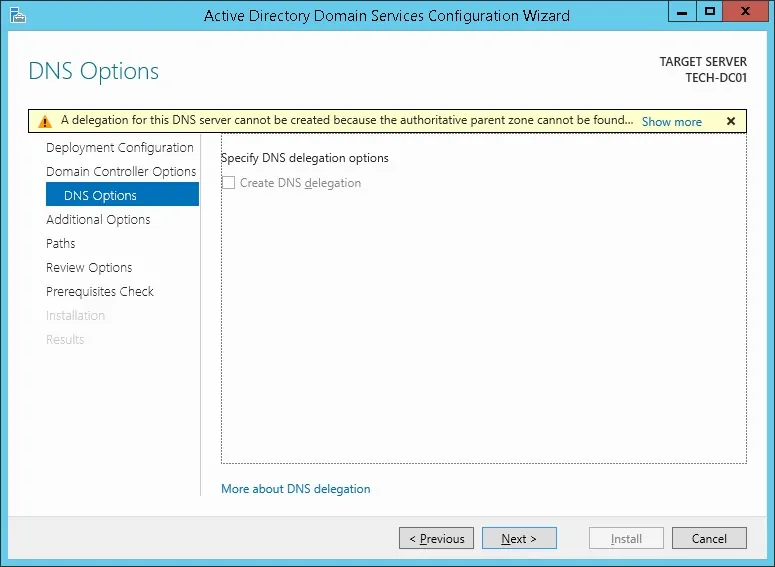
On the DNS options screen, click on the Next button.
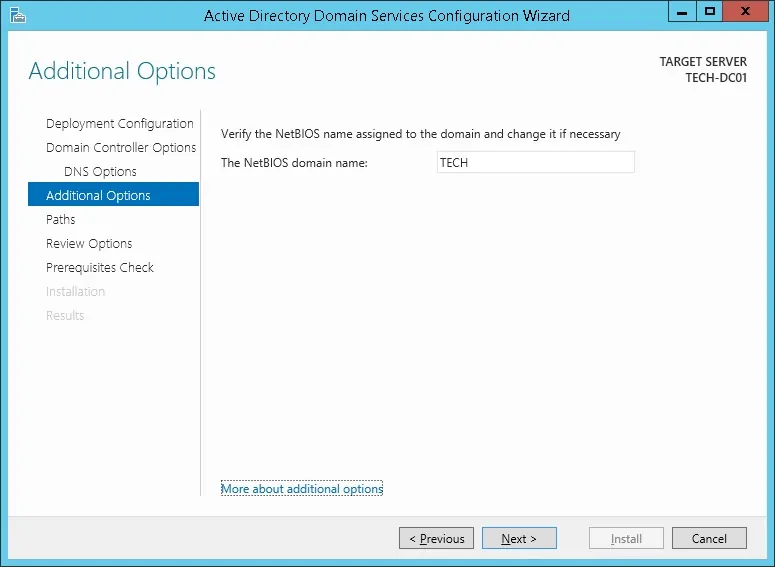
Verify the Netbios name assigned to your domain and click on the Next button.
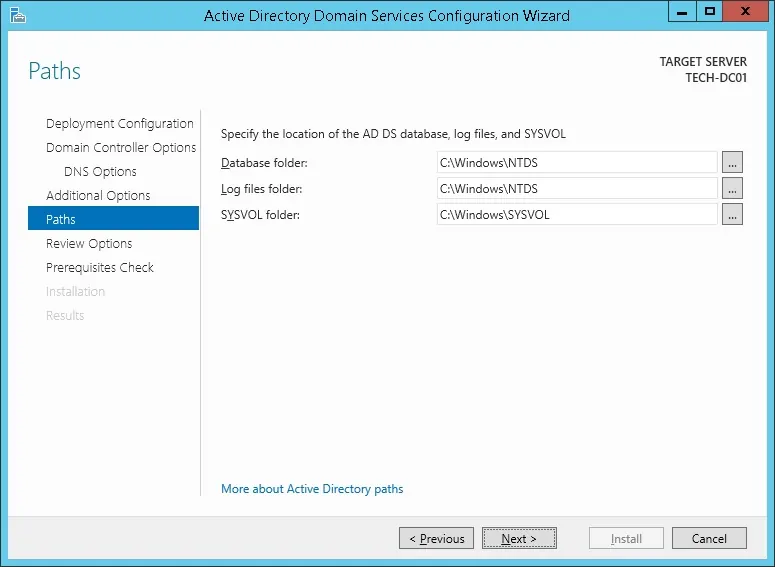
Click on the Next button.
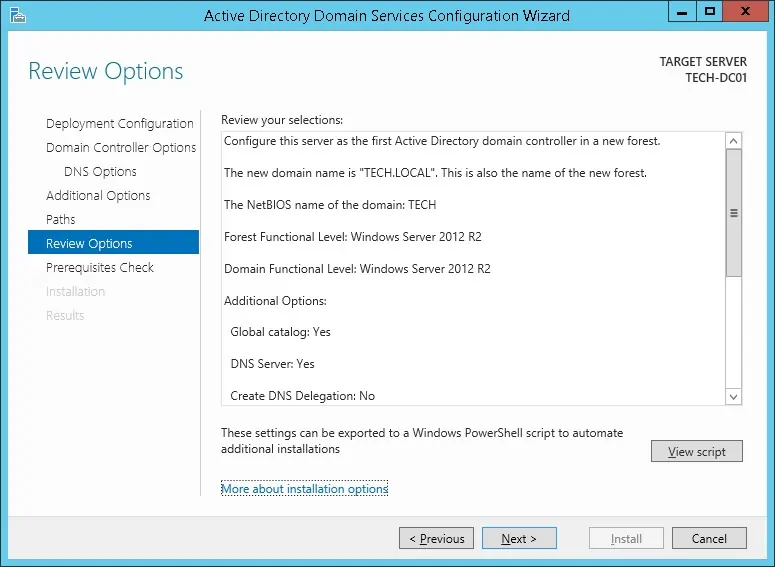
Review your configuration options and click on the Next button.
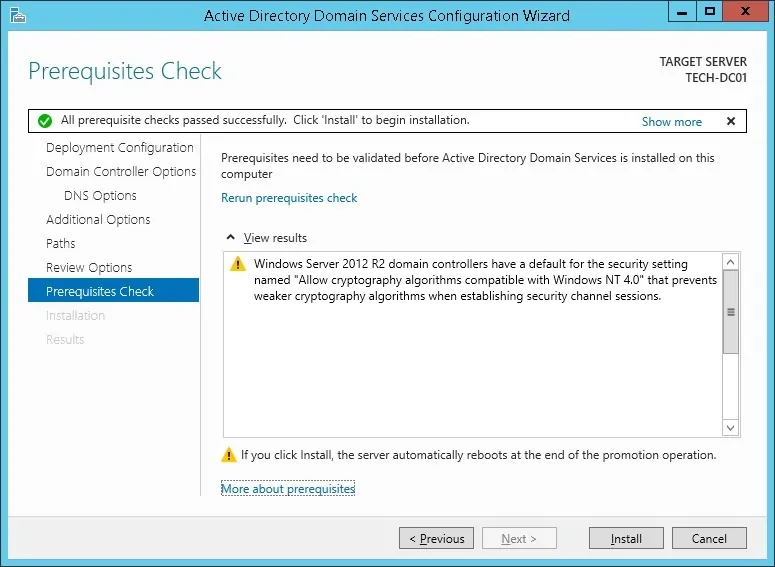
On the Prerequisites Check screen, click on the Install button.
Wait the Active Directory Configuration to finish.
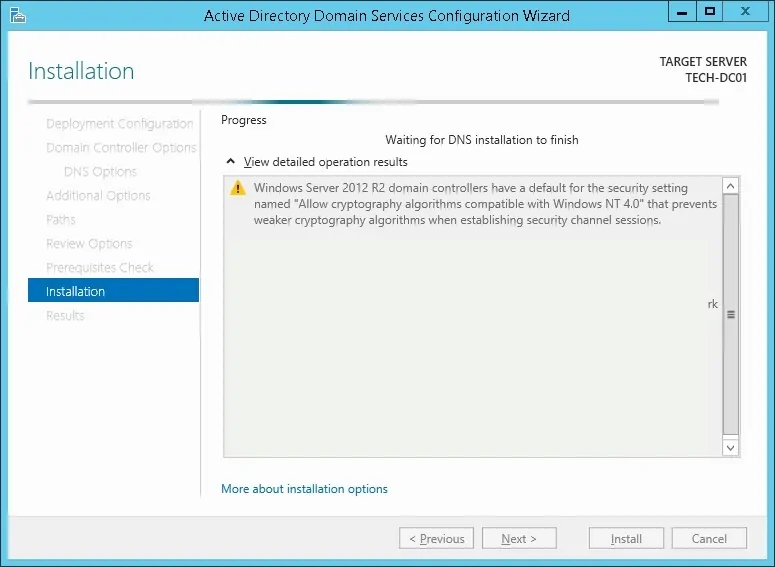
After finishing the Active directory installation, the computer will restart automatically
You have finished the Active directory configuration on Windows server.
Tutorial iDrac - Testing the LDAP over SSL communication
We need to test if your domain controller is offering the LDAP over SSL service on port 636.
On the domain controller, access the start menu and search for the LDP application.
First, let's test if your domain controller is offering the LDAP service on port 389.
Access the Connection menu and select the Connect option.
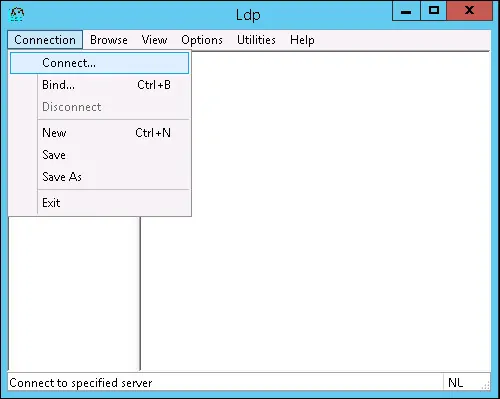
Try to connect to the localhost using the TCP port 389.
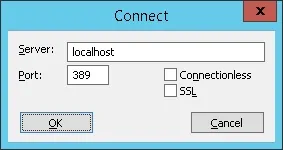
You should be able to connect to the LDAP service on the localhost port 389.
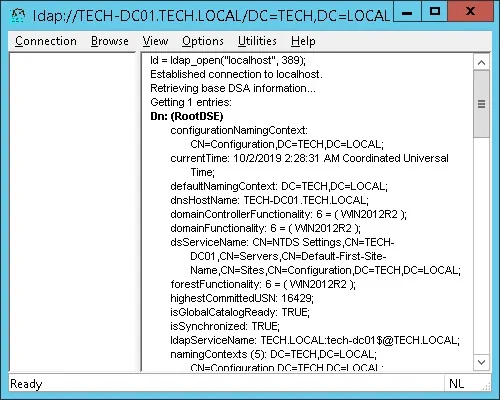
Now, we need to test if your domain controller is offering the LDAP over SSL service on port 636.
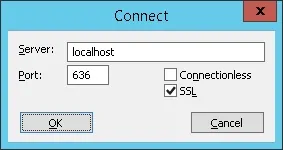
Open a new LDP application Window and try to connect to the localhost using the TCP port 636.
Select the SSL checkbox and click on the Ok button.
If the system displays an error message, your domain controller is not offering the LDAPS service yet.
To solve this, we are going to install a Windows Certification authority on the next part of this tutorial.
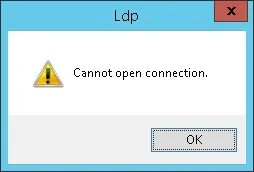
If you were able to successfully connect to the localhost on port 636 using SSL encryption, you may skip the next part of this tutorial.
Tutorial iDrac - Certification Authority Installation on Windows
We need to install the Windows certification authority service.
The local certification authority will provide the domain controller with a certificate that will allow the LDAPS service to operate on the TCP port 636.
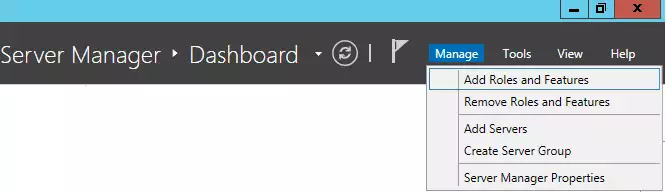
Open the Server Manager application.
Access the Manage menu and click on Add roles and features.
Access the Server role screen, select the Active Directory Certificate Services and click on the Next button.
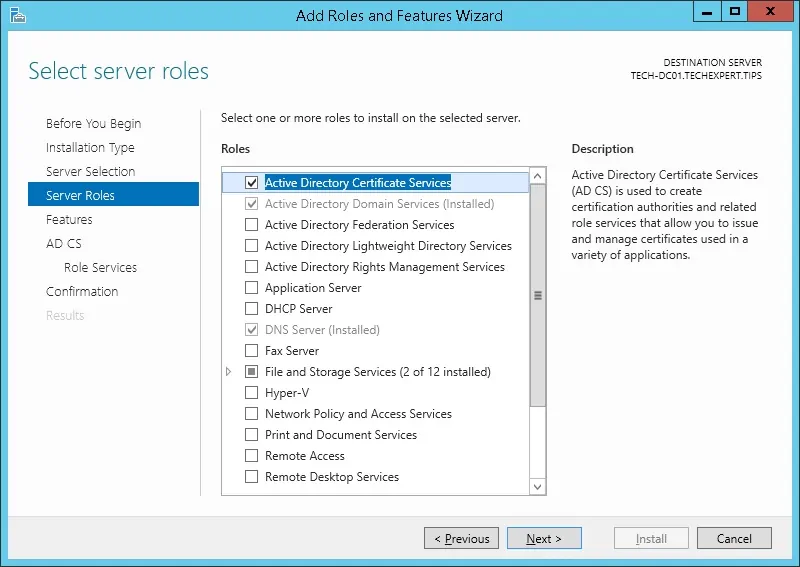
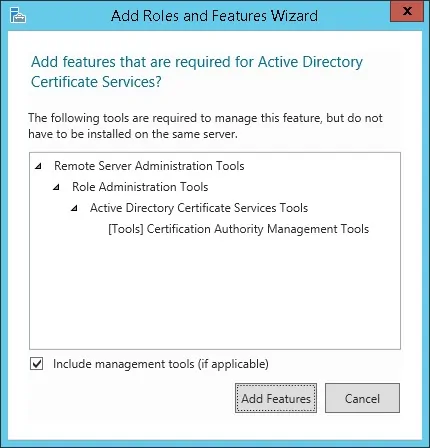
On the following screen, click on the Add features button.
Keep clicking on the Next button until you reach the role service screen.
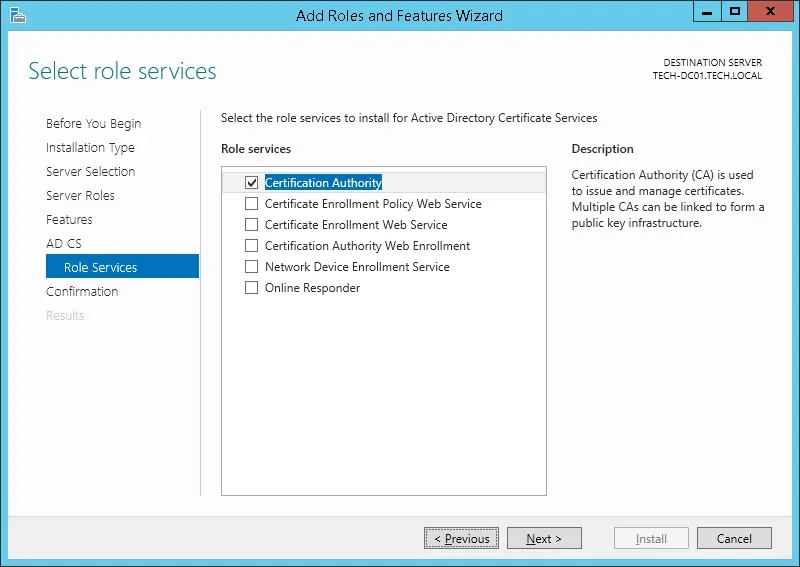
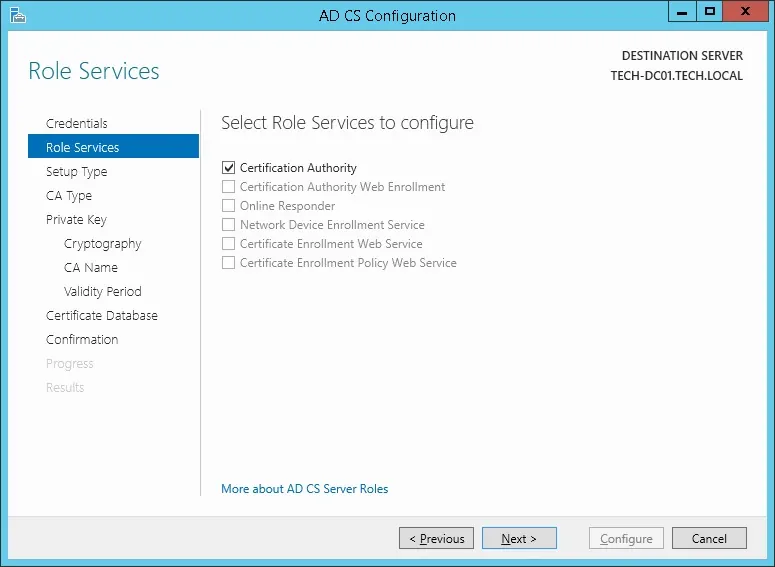
Enable the option named Certification Authority and click on the Next button.
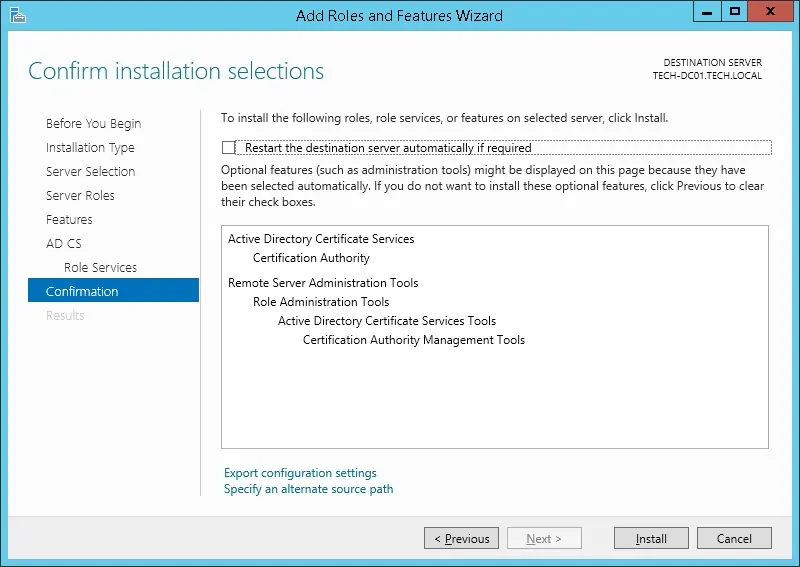
On the confirmation screen, click on the Install button.
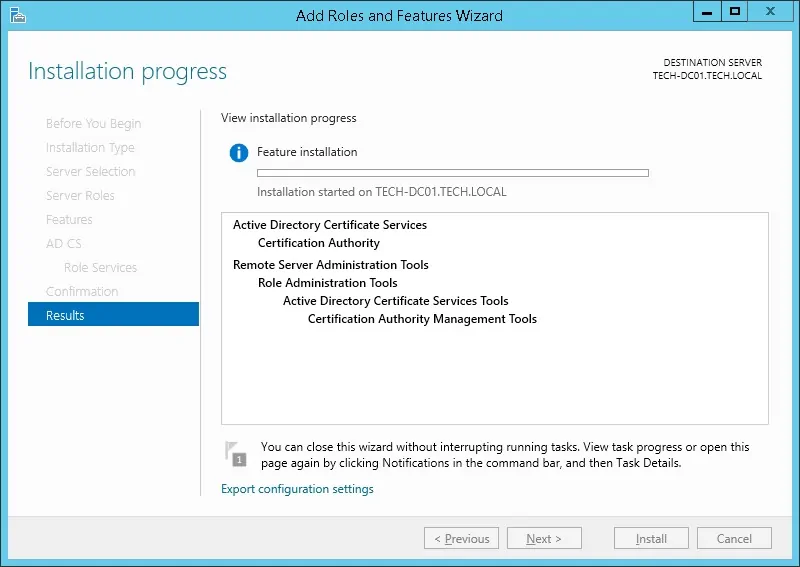
Wait the Certification Authority installation to finish.
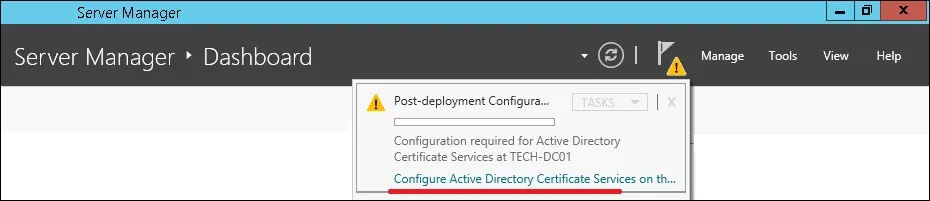
Open the Server Manager application.
Click on the yellow flag menu and select the option: Configure Active Directory Certificate Services
On the credentials screen, click on the Next button.
Select the Certification Authority option and click on the Next button.
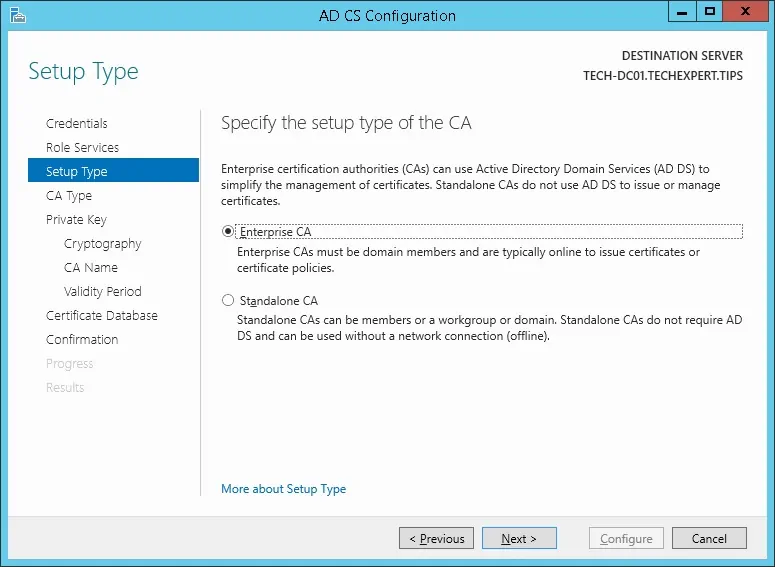
Select the Enterprise CA option and click on the Next button.
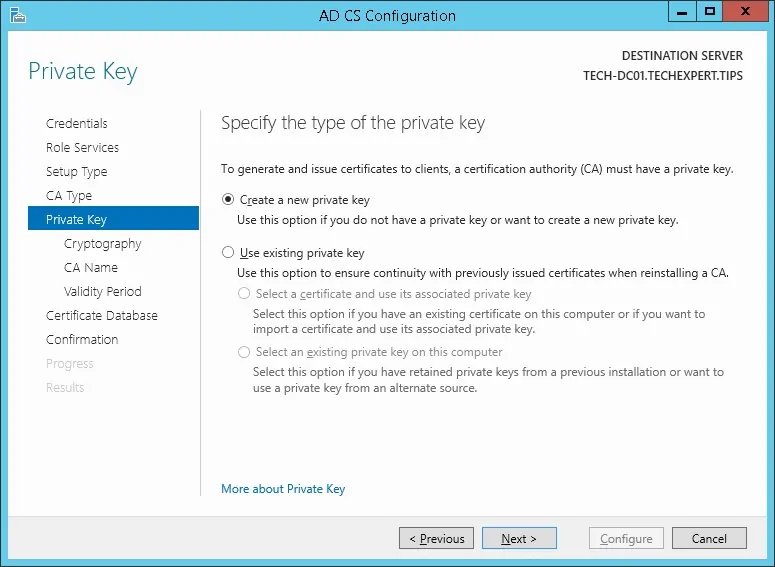
Select the Create a new private key option and click on the Next button.
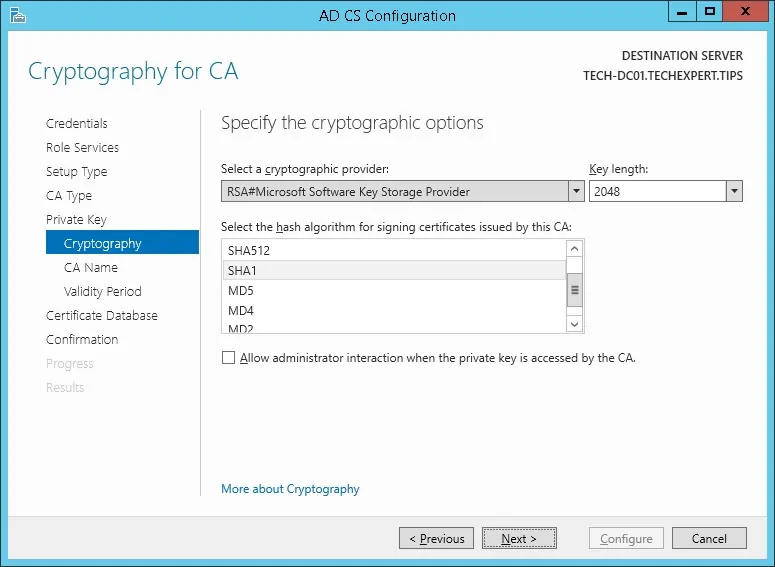
Keep the default cryptography configuration and click on the Next button.
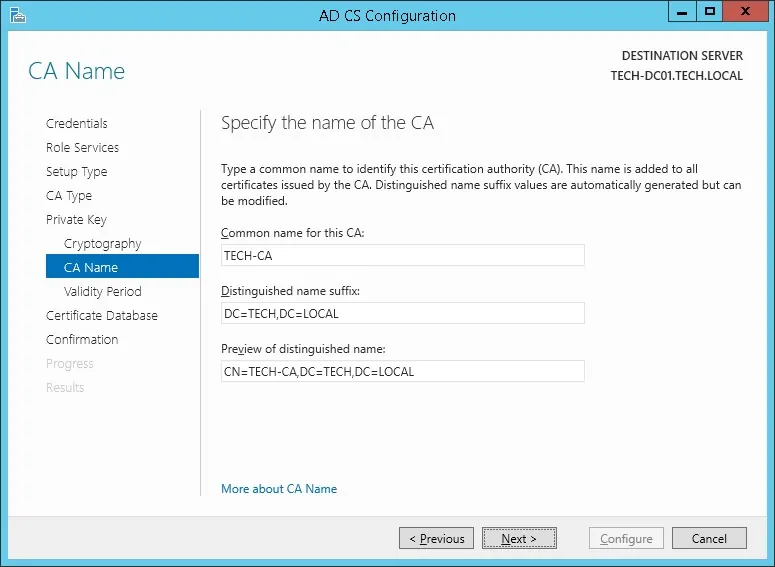
Set a common name to the Certification authority and click on the Next button.
In our example, we set the common name: TECH-CA
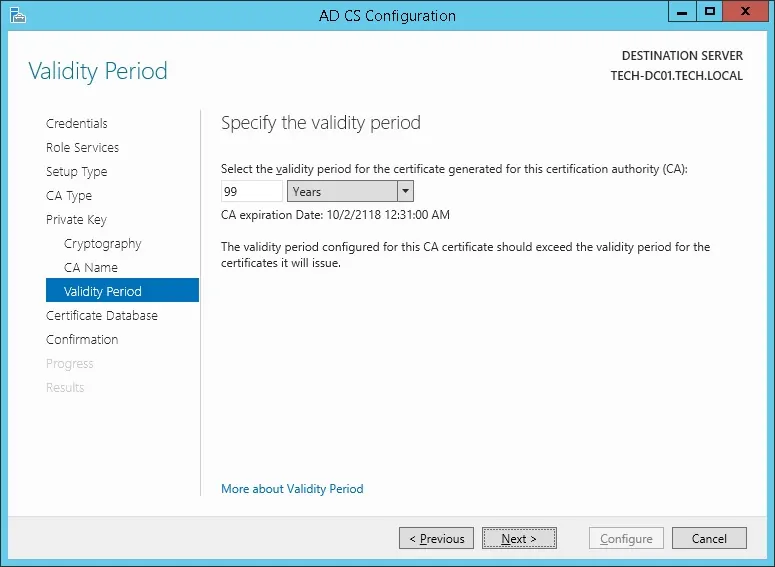
Set the Windows Certification authority validity period.
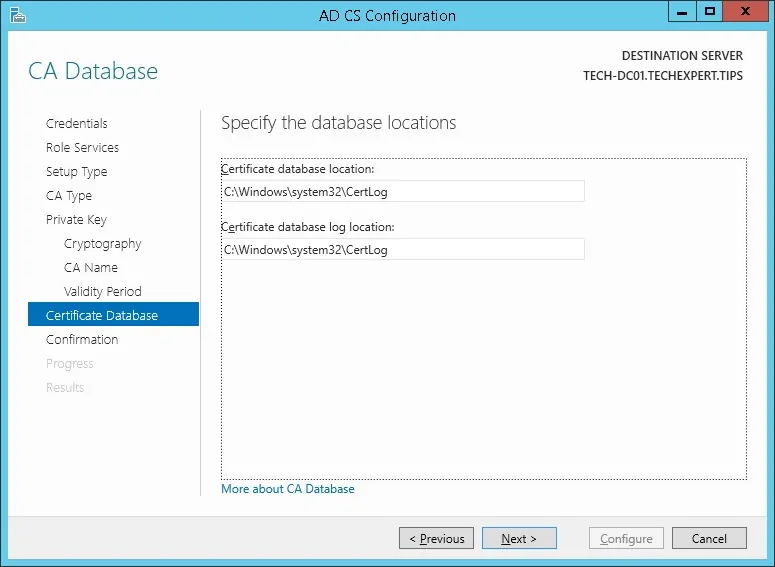
Keep the default Windows Certification authority database location.
Verify the summary and click on the Configure button.
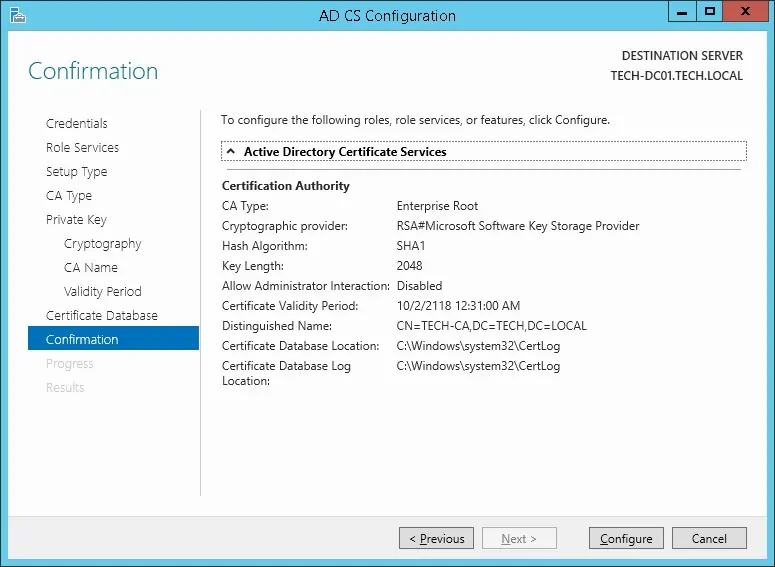
Wait for the Windows server certification authority installation to finish.
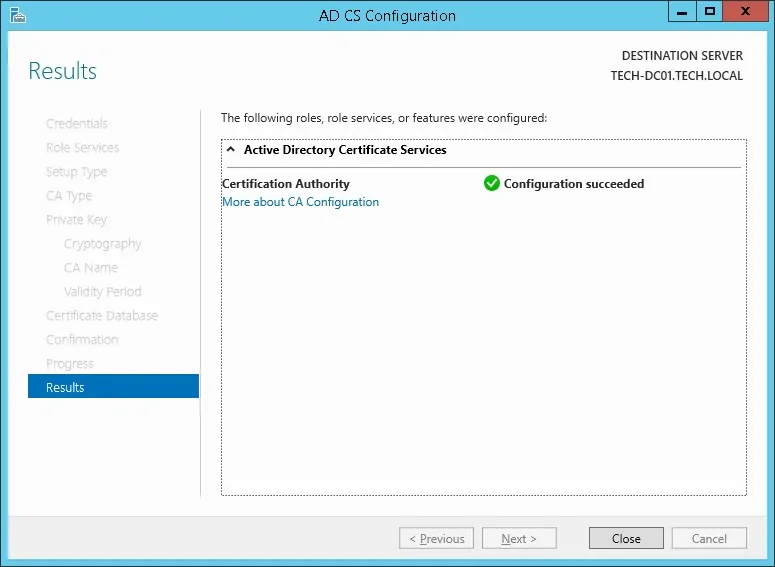
After finishing the certification authority installation, reboot your computer.
You have finished the Windows Certification authority installation.
Tutorial - Testing the LDAP over SSL Communication Again
We need to test if your domain controller is offering the LDAP over SSL service on port 636.
After finishing the Certification authority installation, wait 5 minutes and restart your domain controller.
During boot time, your domain controller will automatically request a server certificate from the local certification authority.
After getting the server certificate, your domain controller will start offering the LDAP service over SSL on the 636 port.
On the domain controller, access the start menu and search for the LDP application.
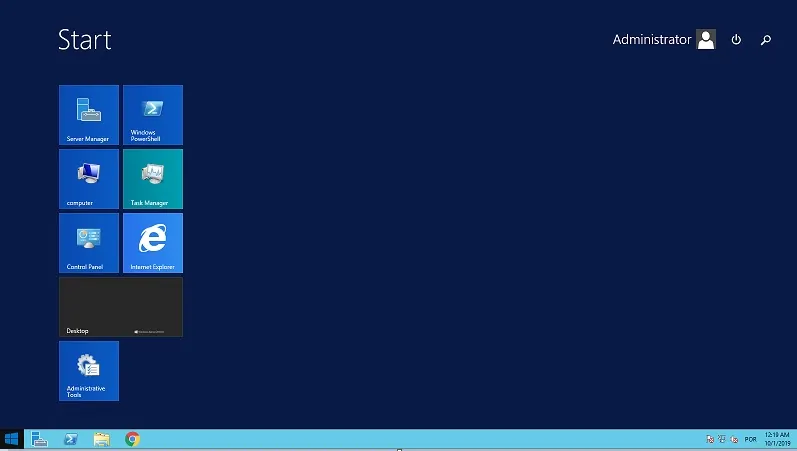
Access the Connection menu and select the Connect option.
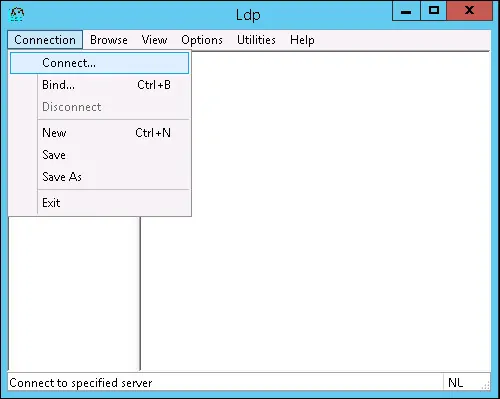
Try to connect to the localhost using the TCP port 636.
Select the SSL checkbox and click on the Ok button.
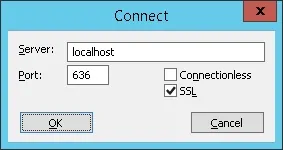
Try to connect to the localhost using the TCP port 636.
Select the SSL checkbox and click on the Ok button.
This time, you should be able to connect to the LDAP service on the localhost port 636.
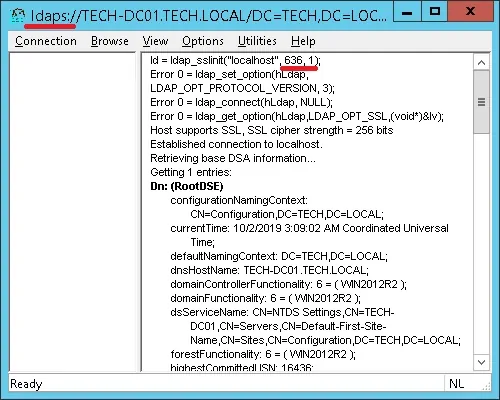
If you are not able to connect to port 636, reboot the computer again and wait 5 minutes more.
It may take sometime before your domain controller receives the certificate requested from the Certification Authority.
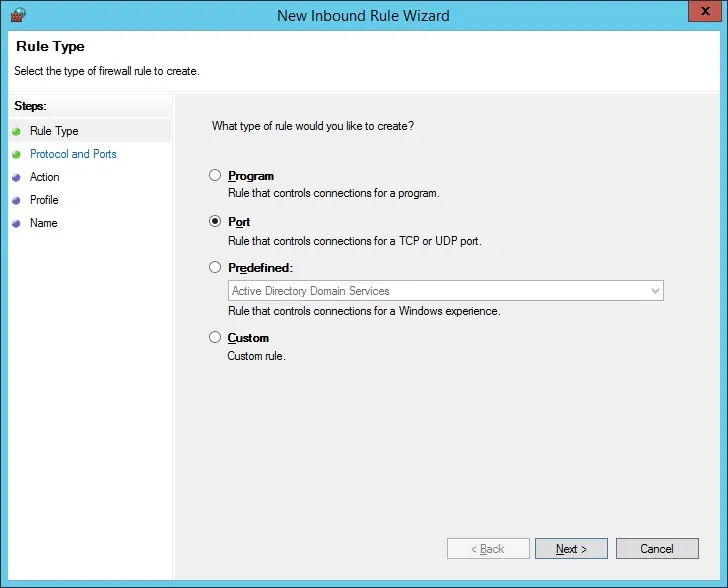
Tutorial - Windows Domain Controller Firewall
We need to create a Firewall rule on the Windows domain controller.
This firewall rule will allow the iDrac interface to query the Active directory database.
On the domain controller, open the application named Windows Firewall with Advanced Security
Create a new Inbound firewall rule.

Select the PORT option.
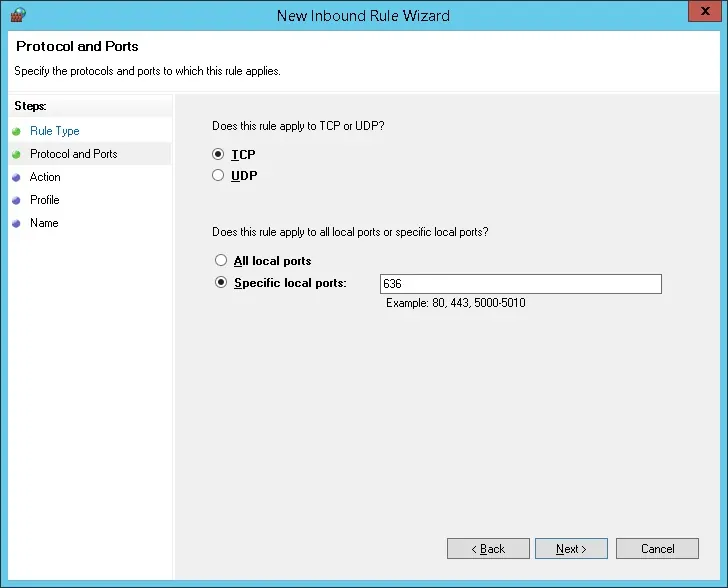
Select the TCP option.
Select the Specific local ports option.
Enter the TCP port 636.
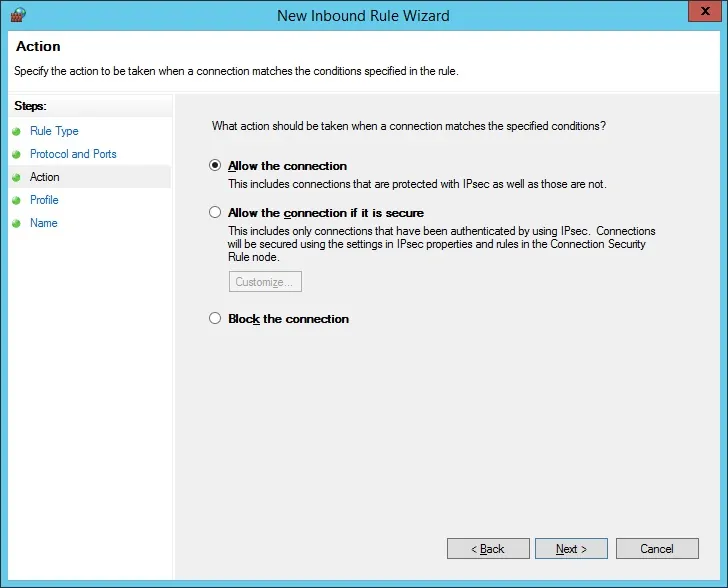
Select the Allow the connection option.
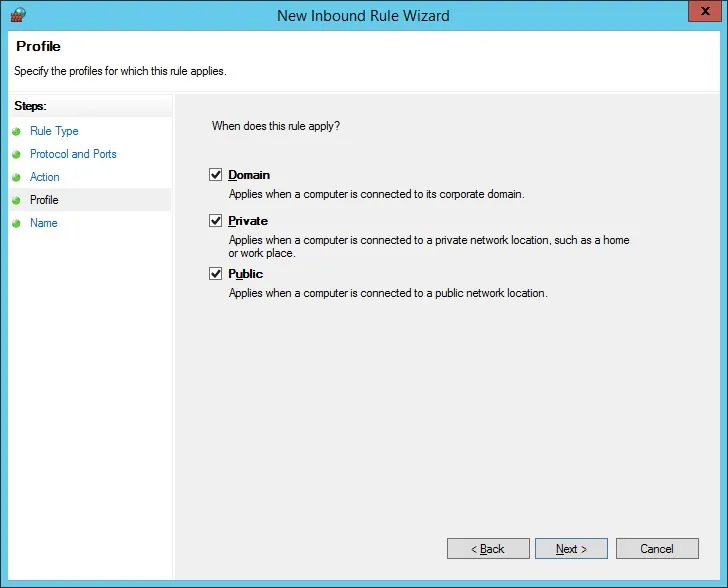
Check the DOMAIN option.
Check the PRIVATE option.
Check the PUBLIC option.
Enter a description to the firewall rule.
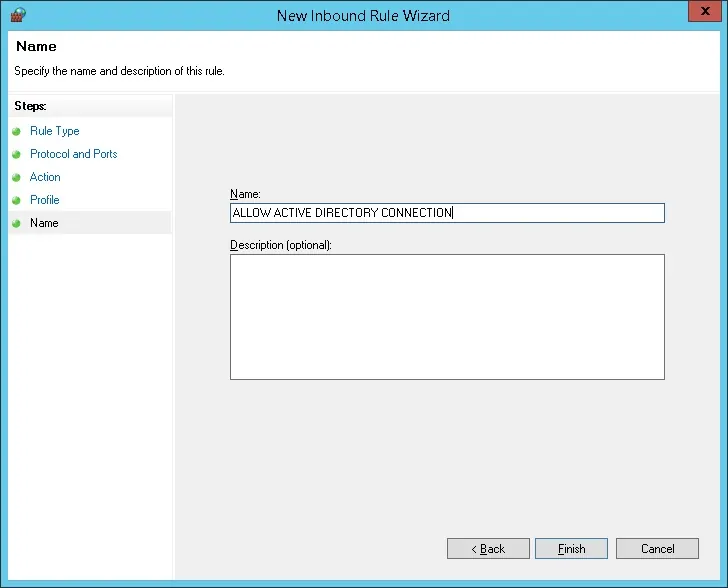
Congratulations, you have created the required firewall rule.
This rule will allow iDrac to query the Active directory database.
Tutorial iDrac - Windows Domain Account Creation
Next, we need to create at least 2 accounts on the Active directory database.
The ADMIN account will be used to login on the iDrac web interface.
The BIND account will be used to query the Active Directory database.
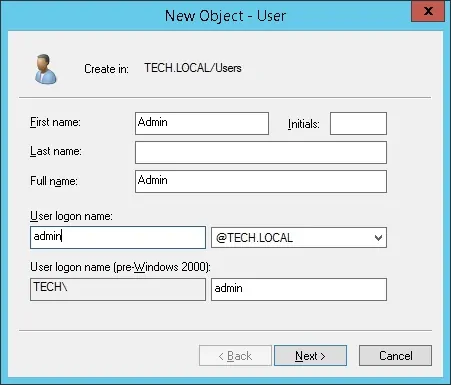
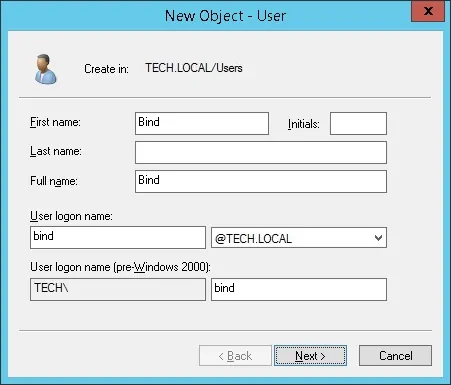
On the domain controller, open the application named: Active Directory Users and Computers
Create a new account inside the Users container.
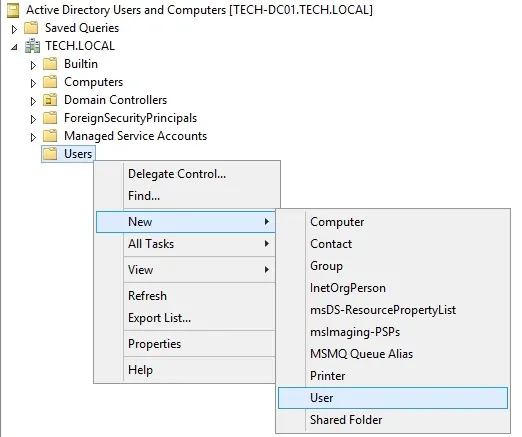
Create a new account named: admin
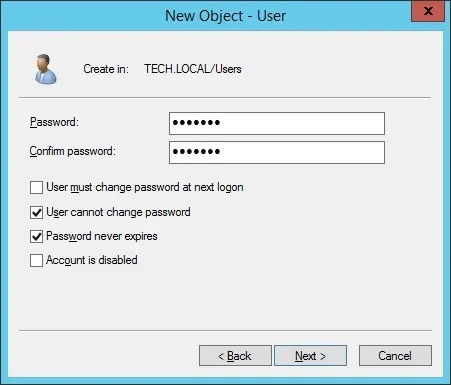
Password configured to the ADMIN user: 123qwe..
This account will be used to authenticate as admin on the iDrac web interface.
Create a new account named: bind
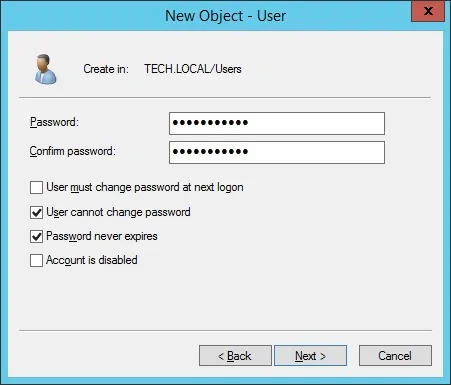
Password configured to the BIND user: 123qwe..
This account will be used to query the passwords stored on the Active Directory database.
Congratulations, you have created the required Active Directory accounts.
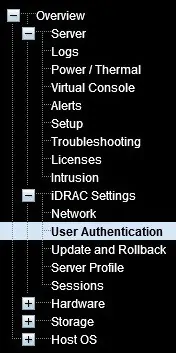
Tutorial - Windows Domain Group Creation
Next, we need to create at least 1 group on the Active directory database.
On the domain controller, open the application named: Active Directory Users and Computers
Create a new group inside the Users container.
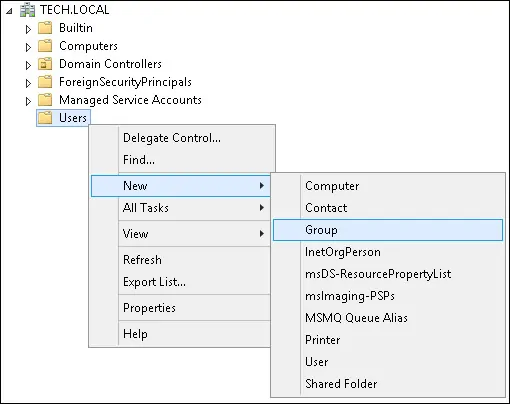
Create a new group named: idrac-admins
Members of this group will have the Admin permission on the iDrac web interface.
Important! Add the admin user as a member of the idrac-admins group.

Congratulations, you have created the required Active Directory group.
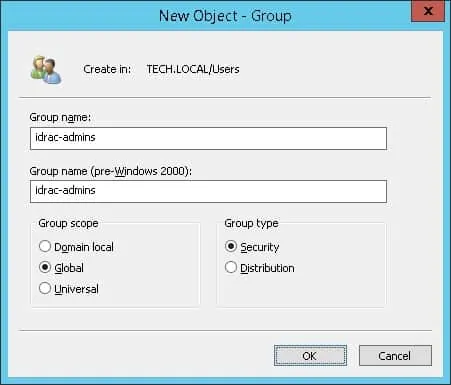
Tutorial - Telnet on iDRAC
Open a browser software, enter the IP address of your iDRAC interface and access the administrative web interface.
On the prompt screen, enter the administrative login information.
Factory default access information:
• Username: root
• Password: calvin
After a successful login, the administrative menu will be displayed.
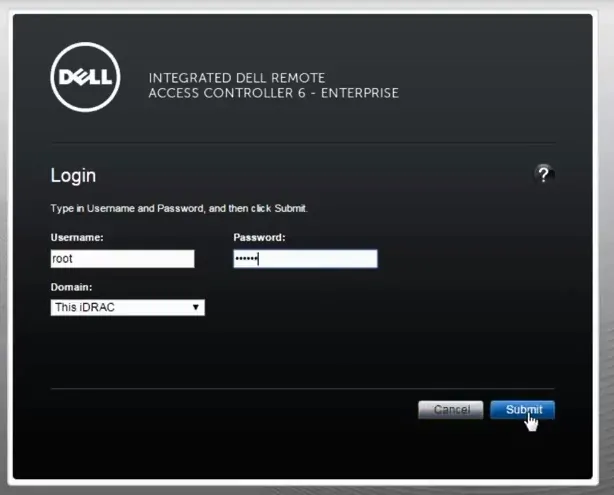
Access the iDRAC settings menu and select the User Authentication option.
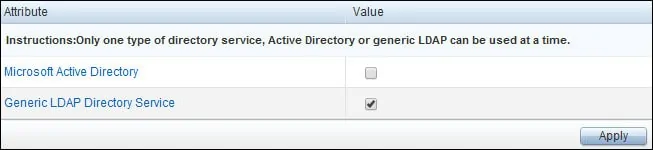
On the top of the screen, access the Directory Services tab.
On the Directory services screen, select the Generic LDAP Directory Service and click on teh Apply button.
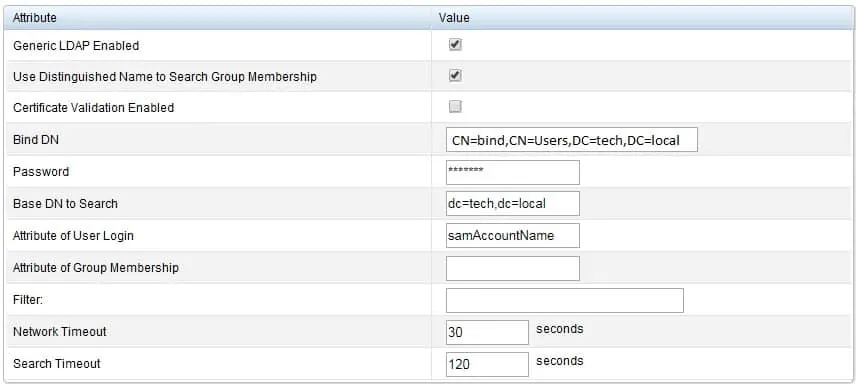
On the Common settings area, perform the following configuration:
• Generic LDAP Enabled: Yes
• Use distinguished name to search group membership: Yes
• Certificate Validation Enabled: No
• Bind DN - CN=bind,CN=Users,DC=tech,DC=local
• Password - Password of the BIND user account
• Base DN to Search: DC=tech,DC=local
• Attribute of User login: samAccountName
You need to change the domain information to reflect your Network environment.
You need to change the bind credentials to reflect your Network environment.
On the LDAP Servers area, perform the following configuration:
• Use static LDAP server: TECH-DC01.TECH.LOCAL
You need to change TECH-DC01.TECH.LOCAL to your domain controller hostname.
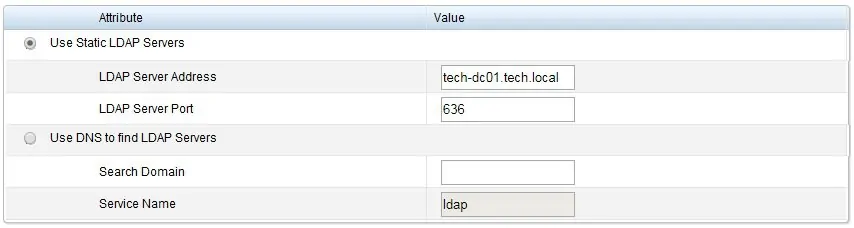
The iDrac interface must be able to translate the LDAP server hostname to the correct IP address.
You need to configure the iDrac interface to use the Active Directory DNS servers.
Optionally, enter a group configuration.
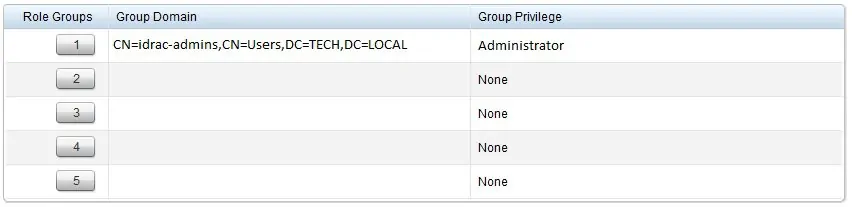
In our example, only members of the idrac-admins group will have the administrative permission.
Congratulations! you have configured the iDrac LDAP authentication to use the Active directory database.
As a test, open a new browser anonymous tab and try to login using the active directory admin account.