Would you like to learn how to configure the PFsense Active directory authentication using Radius? In this tutorial, we are going to show you how to authenticate PFSense users on the Active Directory database using the Radius protocol.
• Pfsense 2.4.4-p3
• Windows 2012 R2
PFsense Related Tutorial:
On this page, we offer quick access to a list of tutorials related to pfSense.
Tutorial - Radius Server Installation on Windows
• IP - 192.168.15.10.
• Operacional System - Windows 2012 R2
• Hostname - TECH-DC01
• Active Directory Domain: TECH.LOCAL
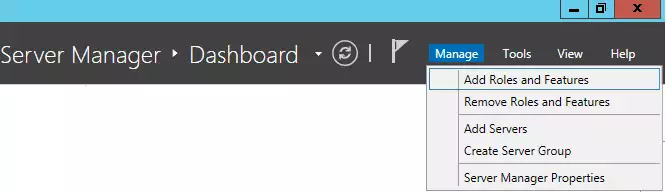
Open the Server Manager application.
Access the Manage menu and click on Add roles and features.
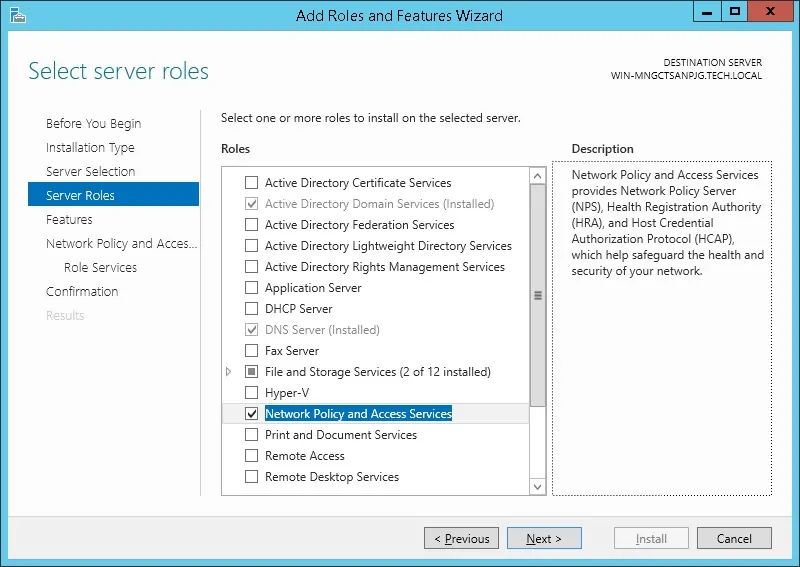
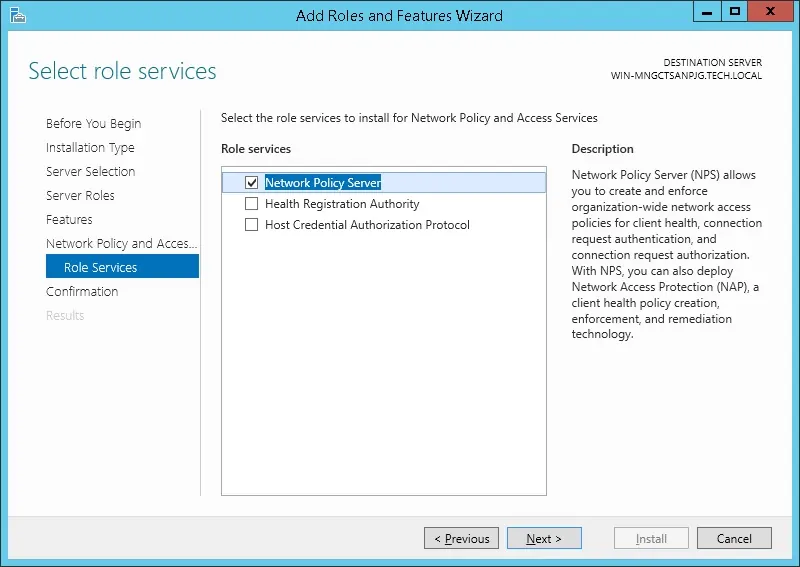
Access the Server roles screen, select the Network Policy and Access Service option.
Click on the Next button.
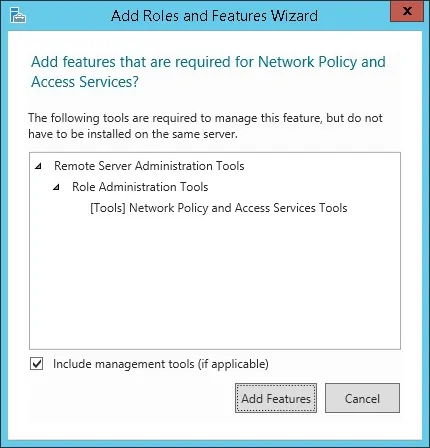
On the following screen, click on the Add features button.
On the Role service screen, click on the Next Button.
On the next screen, click on the Install button.
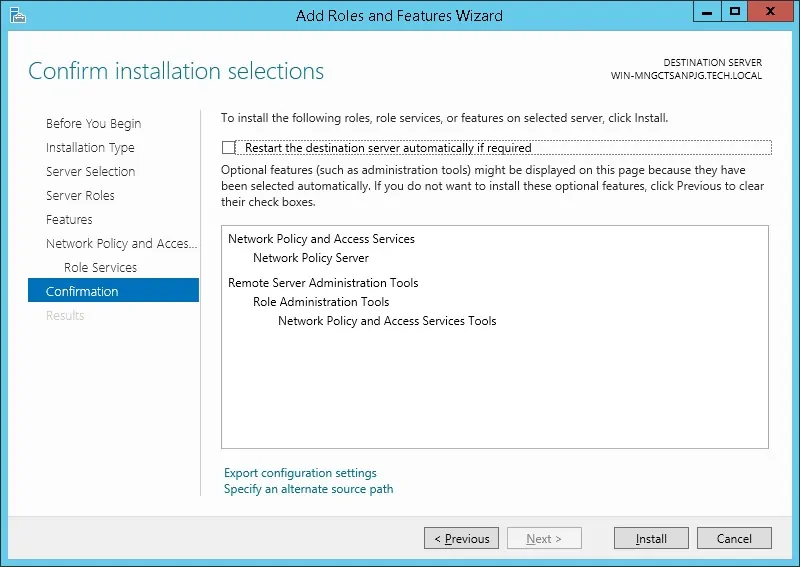
You have finished the Radius server installation on Windows 2012.
Tutorial Radius Server - Active Directory Integration
Next, we need to create at least 1 account on the Active directory database.
The ADMIN account will be used to login on the Pfsense web interface.
On the domain controller, open the application named: Active Directory Users and Computers
Create a new account inside the Users container.
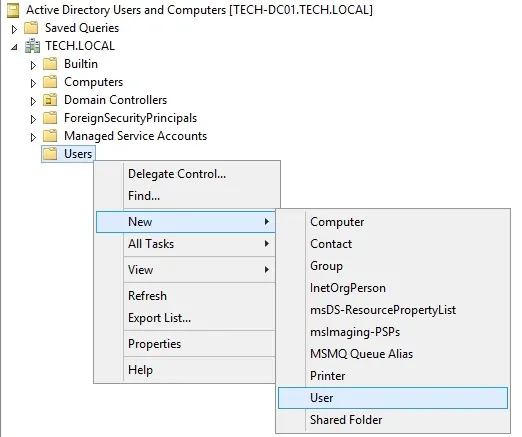
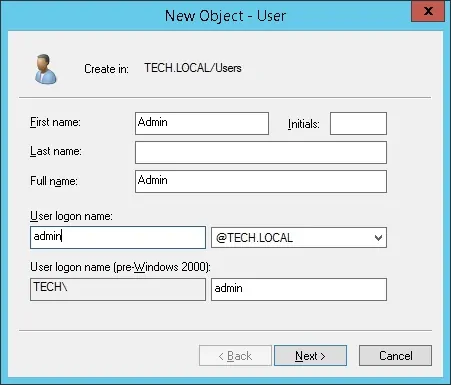
Create a new account named: admin
Password configured to the ADMIN user: 123qwe..
This account will be used to authenticate as admin on the Pfsense web interface.
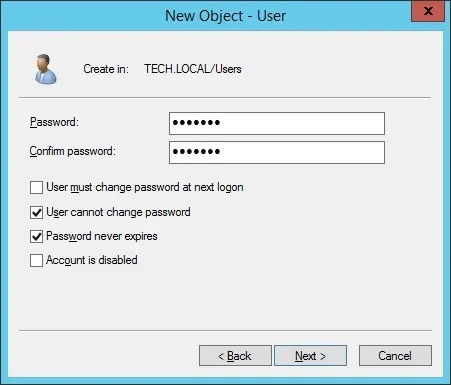
Congratulations, you have created the required Active Directory accounts.
Next, we need to create at least 1 group on the Active directory database.
On the domain controller, open the application named: Active Directory Users and Computers
Create a new group inside the Users container.
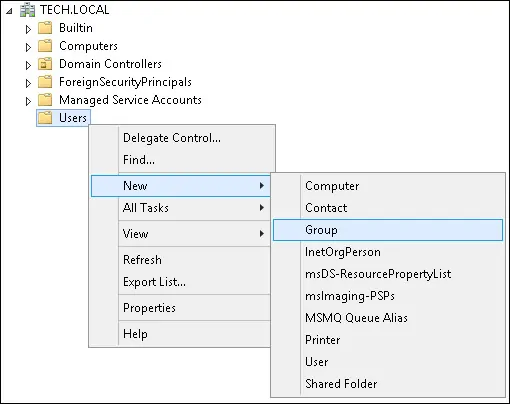
Create a new group named: pfsense-admin
Members of this group will have the Admin permission on the PFsense web interface.
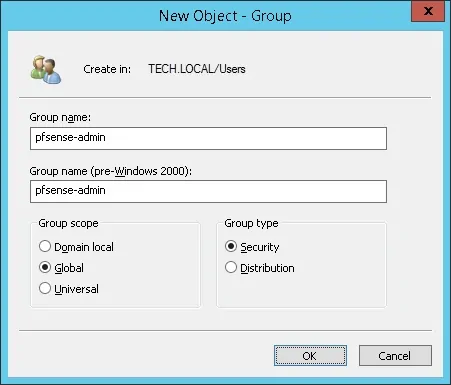
Important! Add the admin user as a member of the pfsense-admin group.

Congratulations, you have created the required Active Directory group.
Tutorial - Windows Domain Controller Firewall
We need to create a Firewall rule on the Windows domain controller.
This firewall rule will allow the Pfsense server to query the Active directory database.
On the domain controller, open the application named Windows Firewall with Advanced Security
Create a new Inbound firewall rule.

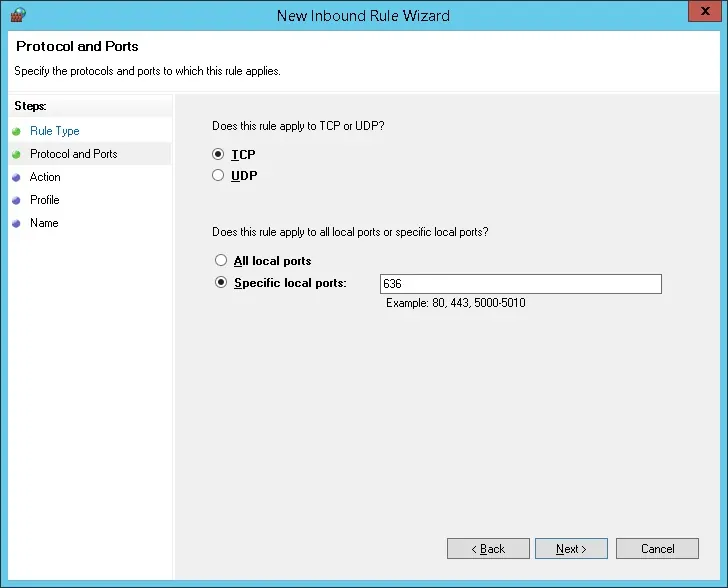
Select the PORT option.
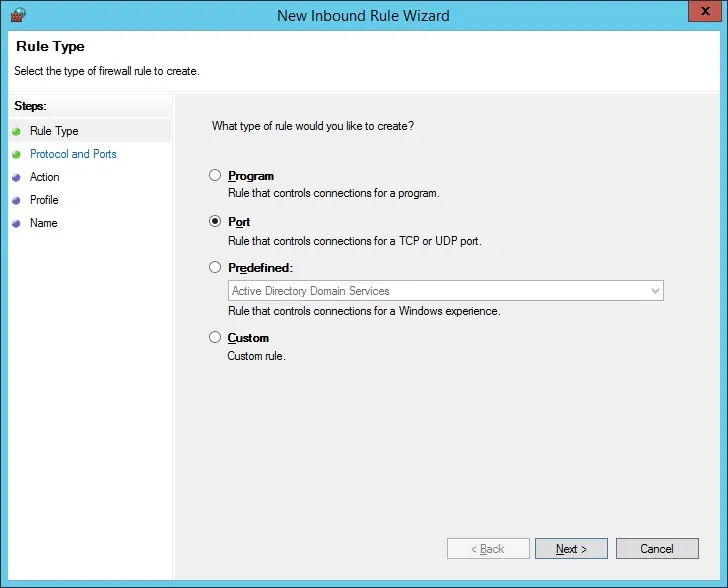
Select the TCP option.
Select the Specific local ports option.
Enter the TCP port 636.
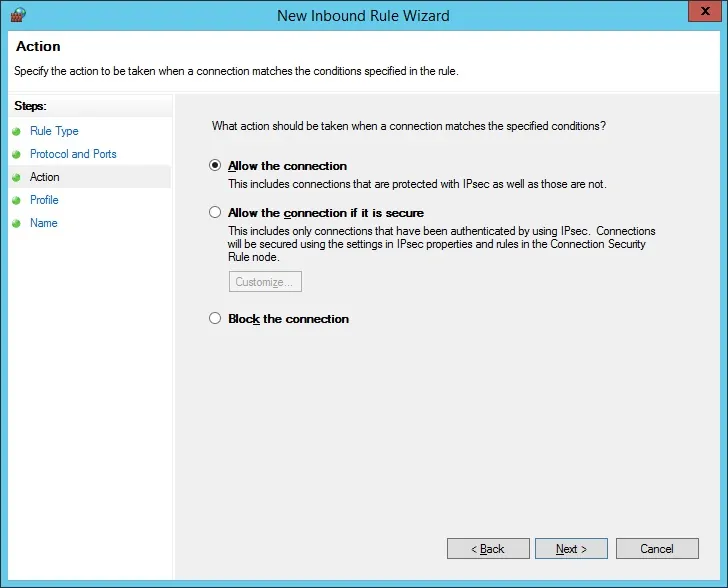
Select the Allow the connection option.
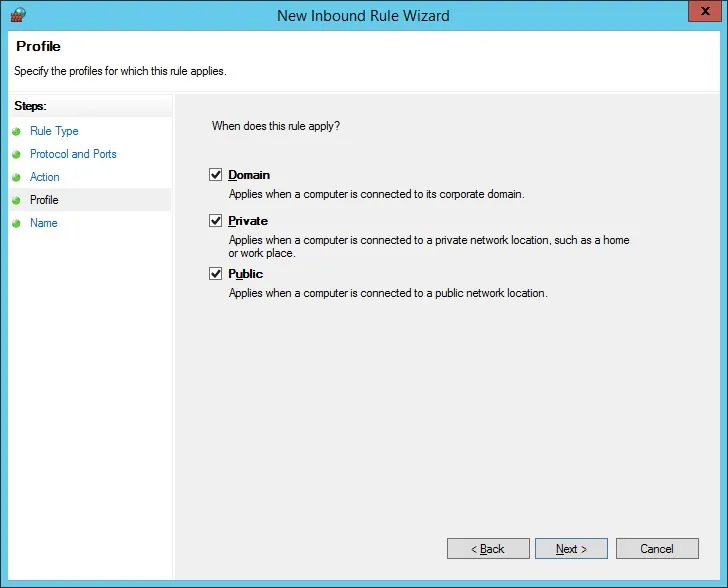
Check the DOMAIN option.
Check the PRIVATE option.
Check the PUBLIC option.
Enter a description to the firewall rule.
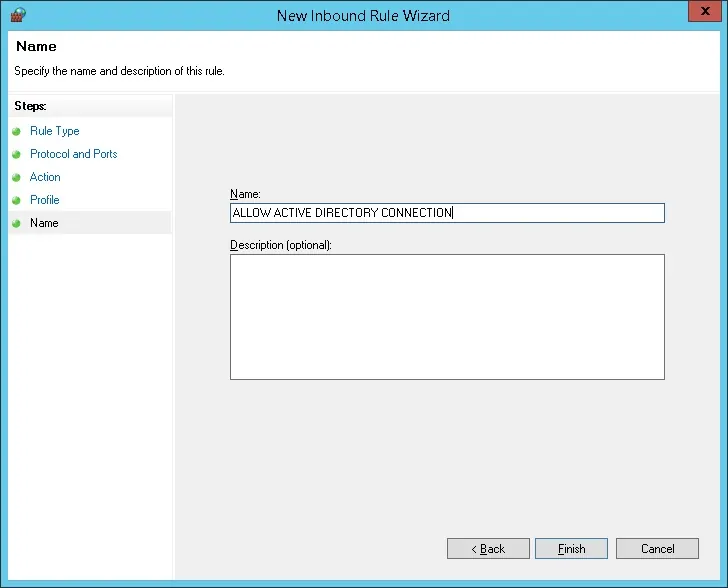
Congratulations, you have created the required firewall rule.
This rule will allow Pfsense to query the Active directory database.
Tutorial Radius Server - Add Client Devices
On the Radius server, open the application named: Network Policy Server
You need to authorize the Radius server on the Active directory database.
Right-click on NPS(LOCAL) and select the Register server in Active Directory option.
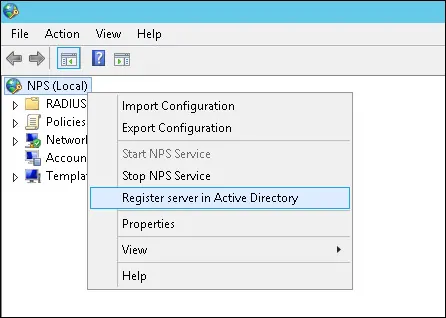
On the confirmation screen, click on the OK button.
Next, you need to configure Radius clients.
Radius clients are devices that will be allowed to request authentication from the Radius server.
Important! Do not confuse Radius clients with Radius users.
Right click on Radius Clients folder and select the New option.
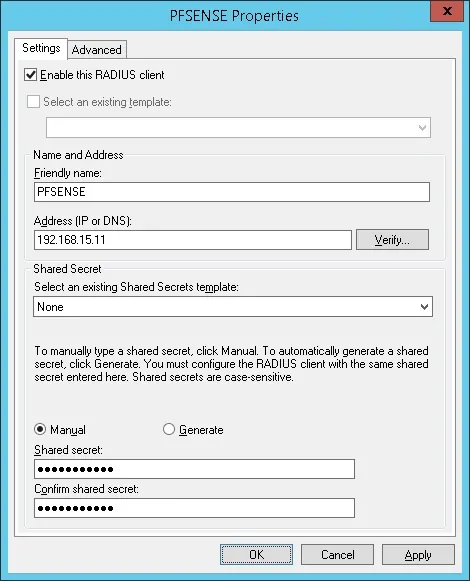
Here is an example of a Client configured to allow a Pfsense firewall to connect to the Radius server.
You need to set the following configuration:
• Friendly name to the device - Add a description to you Pfsense
• Device IP Address - IP address of your PFsense firewall
• Device Shared secret - kamisama123
The Shared secret will be used to authorize the device to use the Radius server.
You have finished the Radius client configuration.
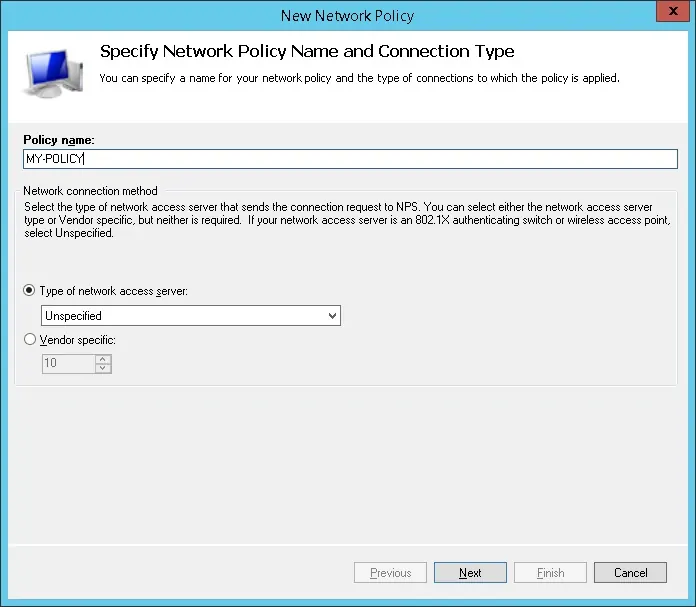
Tutorial Radius Server - Configure a Network Policy
Now, you need to create a Network Polity to allow authentication.
Right click on the Network Policies folder and select the New option.
Enter a name to the network policy and click on the Next button.
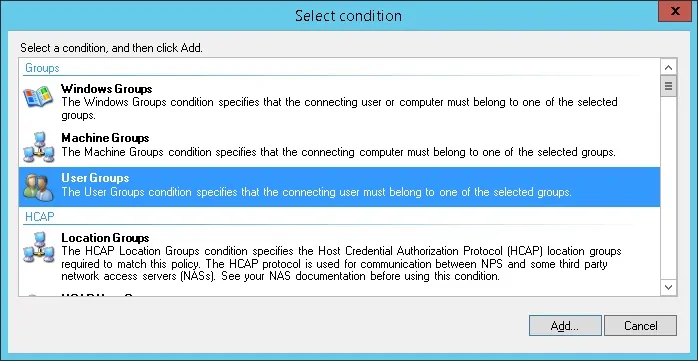
Click on the Add condition button.
We are going to allow members of the PFSENSE-ADMIN group to authenticate.
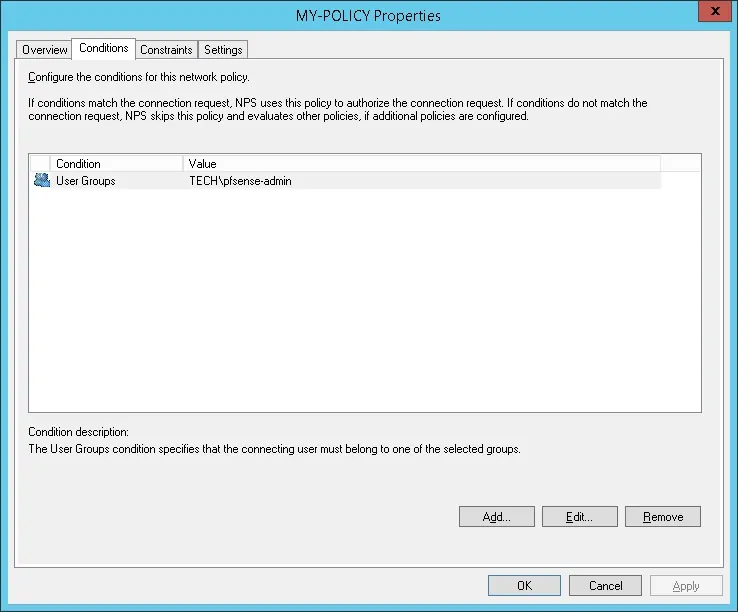
Select the User group option and click on the Add button.
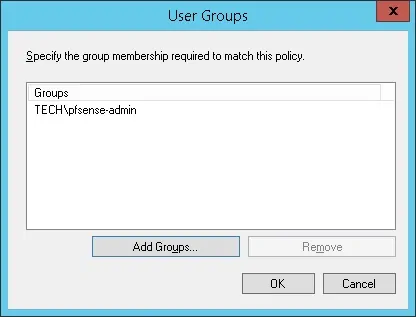
Click on the Add Groups button and locate the PFSENSE-ADMIN group.
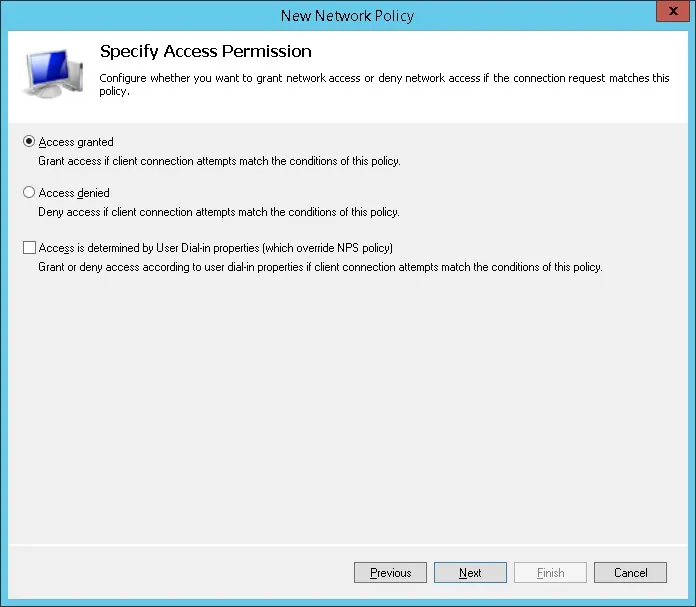
Select the Access granted option and click on the Next button.
This will allow members of the PFSENSE-ADMIN group to authenticate on the Radius server.
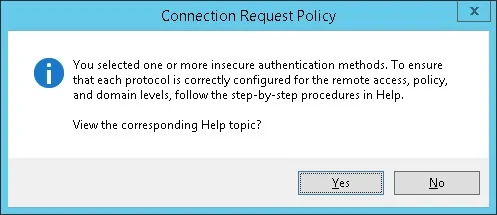
On the Authentication Methods screen, select the Unencrypted authentication (PAP, SPAP) option.
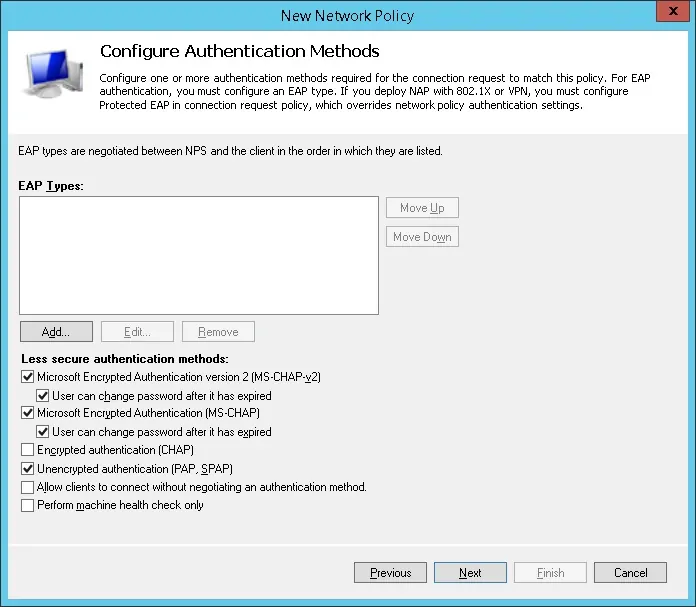
If the following warning is presented, click on the No button.
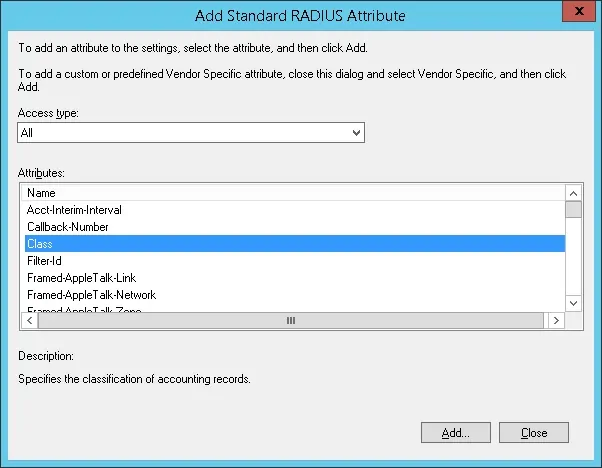
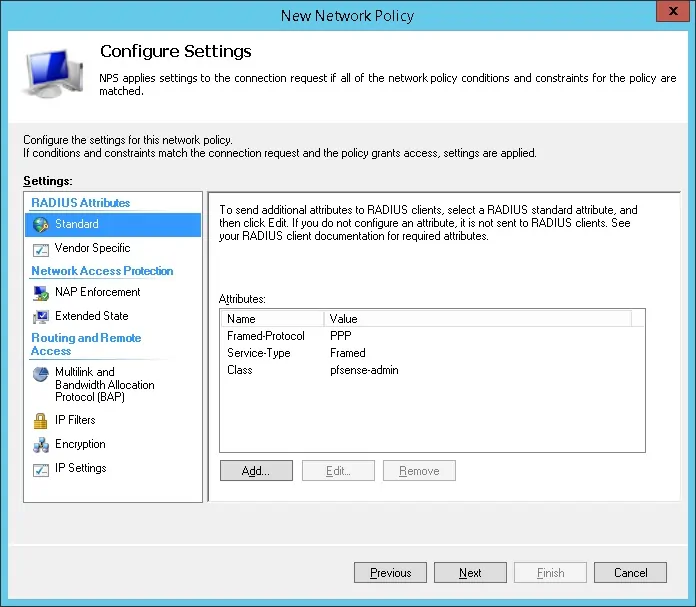
On the Radius configuration screen, select the Standard radius attribute option and click on the Add button
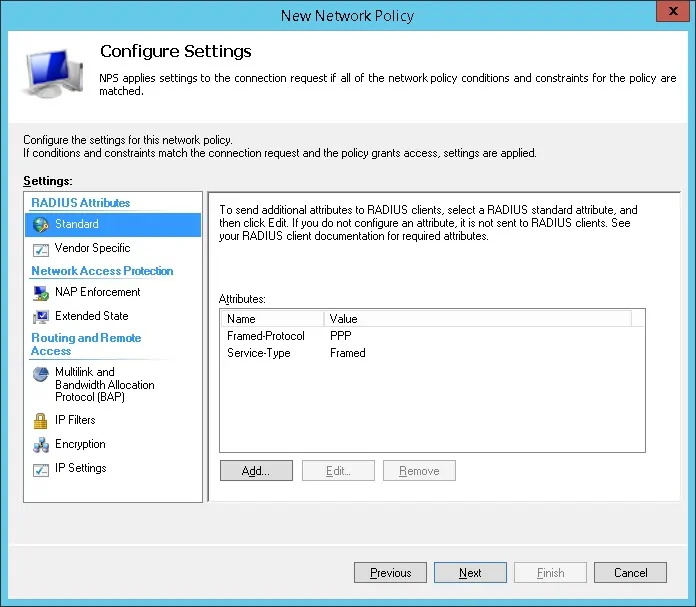
Select the Class attribute and click on the Add button.
Select the String option and enter ten name of the Active group that we created before.
In our example, we created an Active Directory group named PFSENSE-ADMIN.
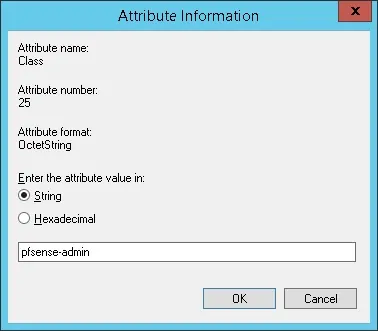
The NPS Radius server will pass the class information back to the PFsense firewall.
The Pfsense firewall will use the class information to set the user as a member of the pfsense-admin group.
Keep in mind that the pfsense-admin group must exist on the active directory and also on the Pfsense firewall.
Verify the Radius server configuration summary and click on the Finish button.
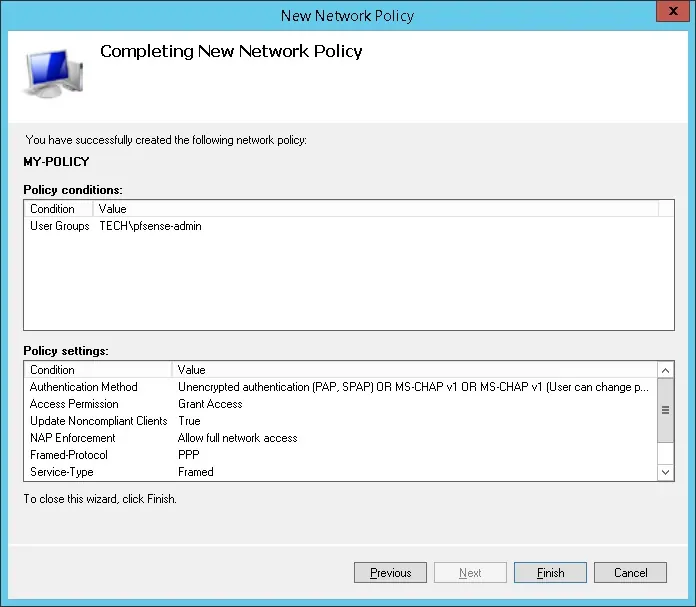
Congratulations! You have finished the Radius server configuration.
PFSense - PFSense Radius Authentication on Active Directory
Open a browser software, enter the IP address of your Pfsense firewall and access web interface.
In our example, the following URL was entered in the Browser:
• https://192.168.15.11
The Pfsense web interface should be presented.
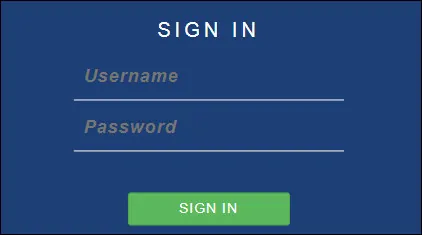
On the prompt screen, enter the Pfsense Default Password login information.
• Username: admin
• Password: pfsense
After a successful login, you will be sent to the Pfsense Dashboard.
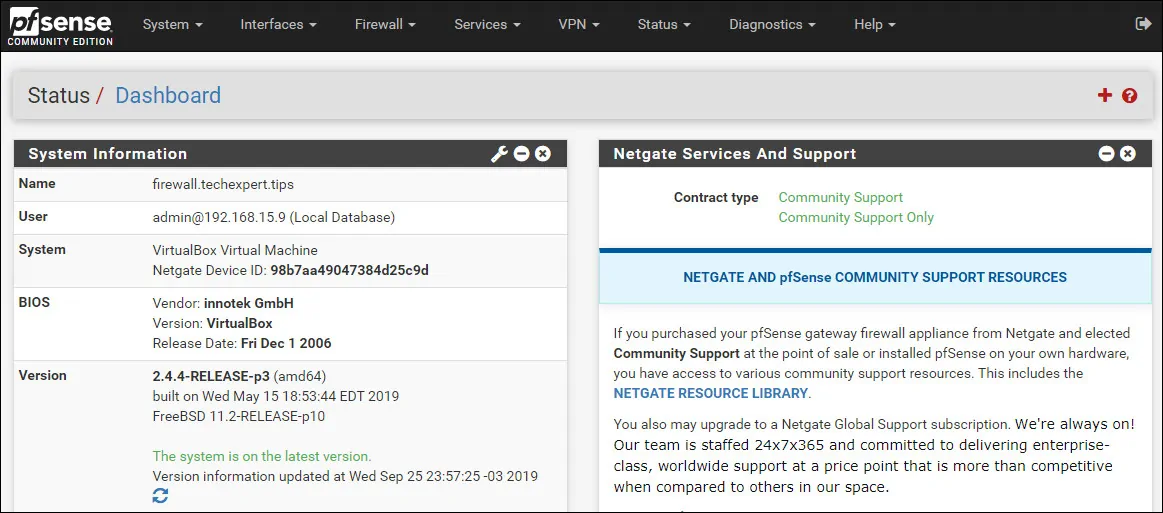
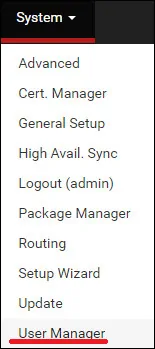
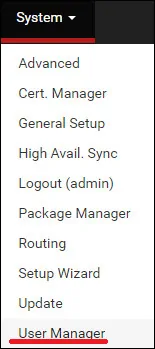
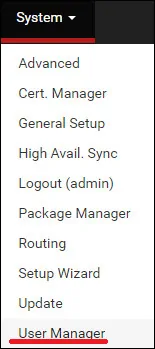
Access the Pfsense System menu and select the User manager option.
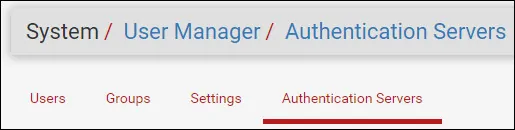
On the User manager screen, access the Authentications servers tab and click on the Add button.
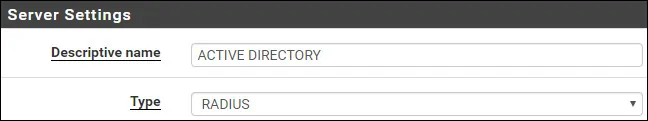
On the Server settings area, perform the following configuration:
• Description name: ACTIVE DIRECTORY
• Type: RADIUS
On the RADIUS Server settings area, perform the following configuration:
• Protocol - PAP
• Hostname or IP address - 192.168.15.10
• Shared Secret - The Radius Client shared secret (kamisama123)
• Services Offered - Authentication and Accounting
• Authentication Port - 1812
• Acconting Port - 1813
• Authentication Timeout - 5
You need to change IP address of the Radius server.
You need to change the Shared secret to reflect your Radius client shared secret.
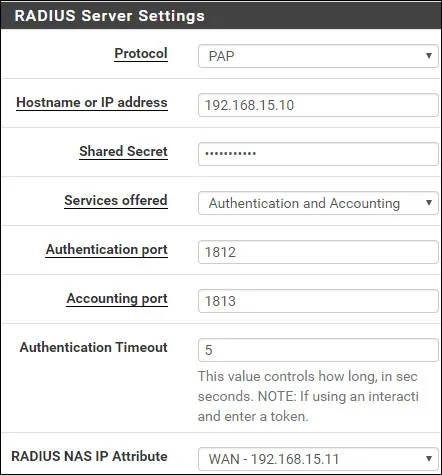
Click on the Save button to finish the configuration.
In our example, we configured the Radius server authentication on the PFSense firewall.
PFSense Radius - Testing Active Directory Authentication
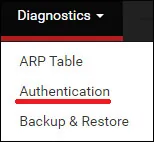
Access the Pfsense Diagnostics menu and select the Authentication option.
Select the Active directory authentication server.
Enter the Admin username, its password and click on the Test button.
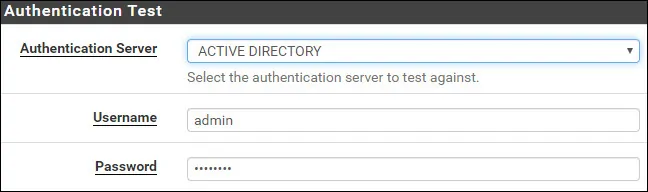
If your test succeeds, you should see the following message.
Congratulations! Your PFsense Radius server authentication on Active Directory was sucessfully configured.
PFSense - Active Directory Group Permission
Access the Pfsense System menu and select the User manager option.
On the User manager screen, access the Groups tab and click on the Add button.
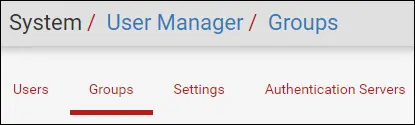
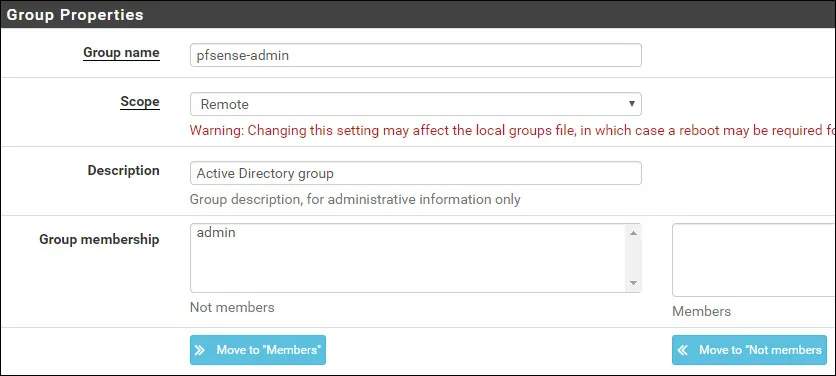
On the Group creation screen, perform the following configuration:
• Group name - pfsense-admin
• Scope - Remote
• Description - Active Directory group
Click on the Save button, you will be sent back to the Group configuration screen.
Now, you need to edit the permissions of the pfsense-admin group.
On the pfsense-admin group properties, locate the Assigned Privileges area and click on the Add button.
On the Group privilege area, perform the following configuration:
• Assigned privileges - WebCfg - All pages
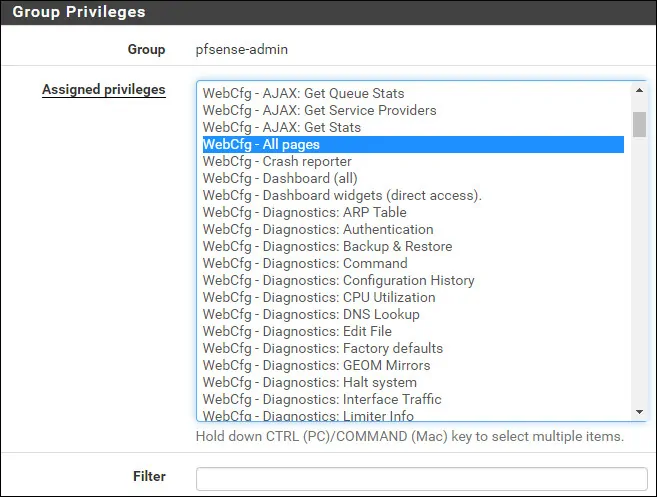
Click on the Save button to finish the configuration.
PFSense - Enable the Active Directory Authentication
Access the Pfsense System menu and select the User manager option.
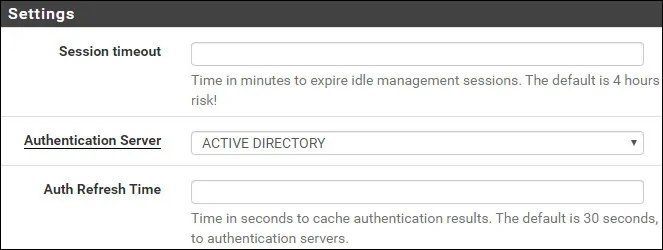
On the User manager screen, access the Settings tab.
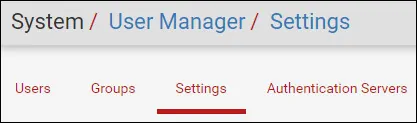
On the Settings screen, select the Active directory authentication server.
Click on the Save and test button.
After finishing your configuration, you should log off the Pfsense web interface.
Try to login using the admin user and the password from the Active Directory database.
On the login screen, use the admin user and the password from the Active Directory database.
• Username: admin
• Password: Enter the Active directory password.
Congratulations! You have configured the PFSense authentication to use the Active Directory database.